 Backend Development
Backend Development PHP Tutorial
PHP Tutorial PHP nginx limits the number of IP requests and the number of concurrency
PHP nginx limits the number of IP requests and the number of concurrencyHow to set a limit on the number of visits to a certain IP within a certain period of time is a headache, especially when facing malicious DDoS attacks. Among them, CC attack (Challenge Collapsar) is a type of DDOS (Distributed Denial of Service) and a common website attack method. The attacker continuously sends a large number of data packets to the victim host through a proxy server or broiler, causing the opponent's server to Resources are exhausted until the machine crashes. CC attacks generally use a limited number of IPs to frequently send data to the server to achieve the purpose of the attack. nginx can limit the number of IP accesses in the same time period through the configuration of HttpLimitReqModul and HttpLimitZoneModule to prevent CC attacks. HttpLimitReqModul is a module used to limit the number of connections per unit time. Use the limit_req_zone and limit_req instructions together to achieve the limit. Once the number of concurrent connections exceeds the specified number, a 503 error will be returned. HttpLimitConnModul is used to limit the number of concurrent connections for a single IP. The difference between the two modules using the limit_zone and limit_conn instructions is that the former limits the number of connections within a period of time, and the latter limits the number of connections at the same time.
HttpLimitReqModul limits the number of instances accessed by the same IP within a certain period of time
<span>http<span>{<span> <span>...<span>
<span>#定义一个名为allips的limit_req_zone用来存储session,大小是10M内存,<span> <span>#以$binary_remote_addr 为key,限制平均每秒的请求为20个,<span> <span>#1M能存储16000个状态,rete的值必须为整数,<span> <span>#如果限制两秒钟一个请求,可以设置成30r/m<span>
limit_req_zone $binary_remote_addr zone<span>=<span>allips<span>:<span>10m<span> rate<span>=<span>20r<span>/<span>s<span>;<span> <span>...<span> server<span>{<span> <span>...<span> location <span>{<span> <span>...<span>
<span>#限制每ip每秒不超过20个请求,漏桶数burst为5<span> <span>#brust的意思就是,如果第1秒、2,3,4秒请求为19个,<span> <span>#第5秒的请求为25个是被允许的。<span> <span>#但是如果你第1秒就25个请求,第2秒超过20的请求返回503错误。<span> <span>#nodelay,如果不设置该选项,严格使用平均速率限制请求数,<span> <span>#第1秒25个请求时,5个请求放到第2秒执行,<span> <span>#设置nodelay,25个请求将在第1秒执行。<span>
limit_req zone<span>=<span>allips burst<span>=<span>5<span> nodelay<span>;<span> <span>...<span> <span>}<span> <span>...<span> <span>}<span> <span>...<span><span>}</span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span>
HttpLimitZoneModule limits the number of concurrent connections
limit_zone can only be defined in the http scope, limit_conn can be defined in the http server location scope
<span>http<span>{<span> <span>...<span>
<span>#定义一个名为one的limit_zone,大小10M内存来存储session,<span> <span>#以$binary_remote_addr 为key<span> <span>#nginx 1.18以后用limit_conn_zone替换了limit_conn<span> <span>#且只能放在http作用域<span> limit_conn_zone one $binary_remote_addr <span>10m<span>;<span>
<span>...<span> server<span>{<span> <span>...<span> location <span>{<span> <span>...<span> limit_conn one <span>20<span>;<span> <span>#连接数限制<span>
<span>#带宽限制,对单个连接限数,如果一个ip两个连接,就是500x2k<span> limit_rate <span>500k<span>;<span>
<span>...<span> <span>}<span> <span>...<span> <span>}<span> <span>...<span><span>}</span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span> nginx whitelist settings
The above configuration will restrict all IPs. Sometimes we don’t want to restrict search engine spiders or test IPs ourselves.
For specific whitelisted IPs, we can use the geo command to achieve this .
1.
<span>http<span>{<span> geo $limited<span>{<span> <span>default<span> <span>1<span>;<span> <span>#google <span> <span>64.233<span>.<span>160.0<span>/<span>19<span> <span>0<span>;<span> <span>65.52<span>.<span>0.0<span>/<span>14<span> <span>0<span>;<span> <span>66.102<span>.<span>0.0<span>/<span>20<span> <span>0<span>;<span> <span>66.249<span>.<span>64.0<span>/<span>19<span> <span>0<span>;<span> <span>72.14<span>.<span>192.0<span>/<span>18<span> <span>0<span>;<span> <span>74.125<span>.<span>0.0<span>/<span>16<span> <span>0<span>;<span> <span>209.85<span>.<span>128.0<span>/<span>17<span> <span>0<span>;<span> <span>216.239<span>.<span>32.0<span>/<span>19<span> <span>0<span>;<span> <span>#M$<span> <span>64.4<span>.<span>0.0<span>/<span>18<span> <span>0<span>;<span> <span>157.60<span>.<span>0.0<span>/<span>16<span> <span>0<span>;<span> <span>157.54<span>.<span>0.0<span>/<span>15<span> <span>0<span>;<span> <span>157.56<span>.<span>0.0<span>/<span>14<span> <span>0<span>;<span> <span>207.46<span>.<span>0.0<span>/<span>16<span> <span>0<span>;<span> <span>207.68<span>.<span>192.0<span>/<span>20<span> <span>0<span>;<span> <span>207.68<span>.<span>128.0<span>/<span>18<span> <span>0<span>;<span> <span>#yahoo<span> <span>8.12<span>.<span>144.0<span>/<span>24<span> <span>0<span>;<span> <span>66.196<span>.<span>64.0<span>/<span>18<span> <span>0<span>;<span> <span>66.228<span>.<span>160.0<span>/<span>19<span> <span>0<span>;<span> <span>67.195<span>.<span>0.0<span>/<span>16<span> <span>0<span>;<span> <span>74.6<span>.<span>0.0<span>/<span>16<span> <span>0<span>;<span> <span>68.142<span>.<span>192.0<span>/<span>18<span> <span>0<span>;<span> <span>72.30<span>.<span>0.0<span>/<span>16<span> <span>0<span>;<span> <span>209.191<span>.<span>64.0<span>/<span>18<span> <span>0<span>;<span> <span>#My IPs<span> <span>127.0<span>.<span>0.1<span>/<span>32<span> <span>0<span>;<span> <span>123.456<span>.<span>0.0<span>/<span>28<span> <span>0<span>;<span> <span>#example for your server CIDR<span> <span>}</span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span>
geo directive defines a whitelist $limited variable, the default value is 1, if the client IP is within the above range, the value of $limited is 0
2. Use the map directive to map the search engine client The ip is an empty string. If it is not a search engine, the real ip will be displayed. In this way, the search engine ip cannot be stored in the limit_req_zone memory session, so the search engine’s ip access will not be restricted.
map $limited $limit {
1 $binary_remote_addr ;
0 "";
}
3. Set limit_req_zone and limit_req
limit_req_zone $limit z rate=10r/m;
limit_req z burst=5;
Finally we use ab to suppress php-fpm, for the above The effect of the method is actually tested
Example 1: The restriction only allows one IP to access the configuration 60 times in one minute, which is an average of 1 time per second
First we prepare a php script and place it in the root directory $document_root
test. php
nginx configuration added limit_req_zone and limit_req
<span>http<span>{<span> <span>...<span> limit_req_zone $binary_remote_addr zone<span>=<span>allips<span>:<span>10m<span> rate<span>=<span>60r<span>/<span>m<span>;<span> <span>...<span> server<span>{<span> <span>...<span> location <span>{<span> <span>...<span> limit_req zone<span>=<span>allips<span>;<span> <span>...<span> <span>}<span> <span>...<span> <span>}<span> <span>...<span><span>}</span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span>
ab -n 5 -c 1 http://www.weizhang.org/test.php
118.144.94.193 - - [22/Dec/2012: 06:27:06 +0000] "GET /test.php HTTP/1.0" 200 11000 "-" "ApacheBench/2.3"
118.144.94.193 - - [22/Dec/2012:06:27:06 +0000] " GET /test.php HTTP/1.0" 503 537 "-" "ApacheBench/2.3"
118.144.94.193 - - [22/Dec/2012:06:27:07 +0000] "GET /test.php HTTP/1.0" 503 537 "-" "ApacheBench/2.3"
118.144.94.193 - - [22/Dec/2012:06:27:07 +0000] "GET /test.php HTTP/1.0" 503 537 "-" "ApacheBench/2.3 "
118.144.94.193 - - [22/Dec/2012:06:27:07 +0000] "GET /test.php HTTP/1.0" 503 537 "-" "ApacheBench/2.3"
It is ok if brust and nodelay are not set Seeing that this configuration only allows 1 access per second, excessive requests return a 503 error
<span>http<span>{<span> <span>...<span> limit_req_zone $binary_remote_addr zone<span>=<span>allips<span>:<span>10m<span> rate<span>=<span>60r<span>/<span>m<span>;<span> <span>...<span> server<span>{<span> <span>...<span> location <span>{<span> <span>...<span> limit_req zone<span>=<span>allips burst<span>=<span>1<span> nodelay<span>;<span> <span>...<span> <span>}<span> <span>...<span> <span>}<span> <span>...<span><span>}</span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span>
ab -n 5 -c 1 http://www.weizhang.org/test.php
118.144.94.193 - - [22 /Dec/2012:07:01:00 +0000] "GET /test.php HTTP/1.0" 200 11000 "-" "ApacheBench/2.3"
118.144.94.193 - - [22/Dec/2012:07:01: 00 +0000] "GET /test.php HTTP/1.0" 200 11000 "-" "ApacheBench/2.3"
118.144.94.193 - - [22/Dec/2012:07:01:01 +0000] "GET /test. php HTTP/1.0" 503 537 "-" "ApacheBench/2.3"
118.144.94.193 - - [22/Dec/2012:07:01:01 +0000] "GET /test.php HTTP/1.0" 503 537 "- " "ApacheBench/2.3"
118.144.94.193 - - [22/Dec/2012:07:01:01 +0000] "GET /test.php HTTP/1.0" 503 537 "-" "ApacheBench/2.3"
Settings After brust=1 and nodelay, two requests are allowed to be processed in the first second.
The above introduces how PHP nginx limits the number of IP requests and the number of concurrency, including the content. I hope it will be helpful to friends who are interested in PHP tutorials.
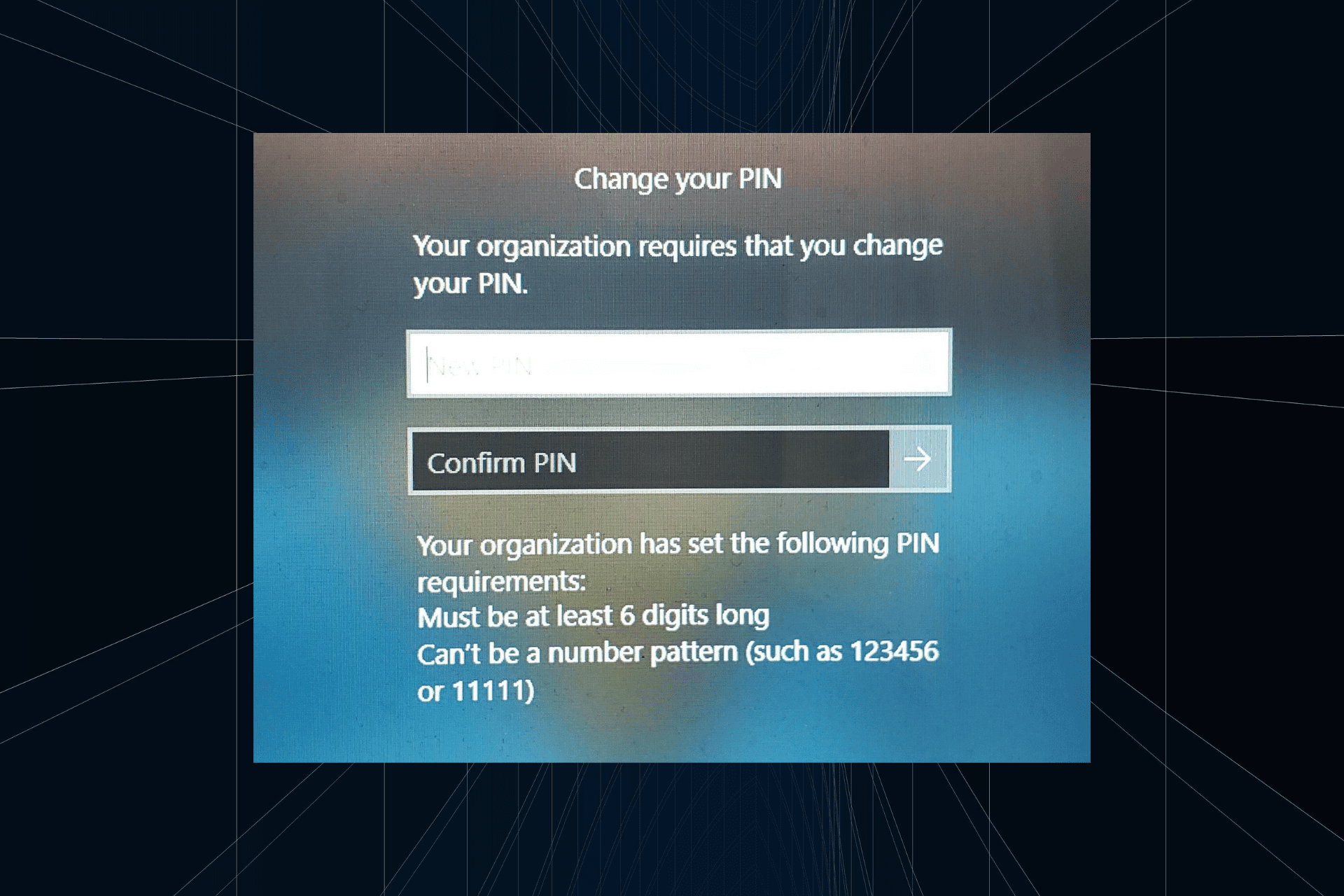 解决方法:您的组织要求您更改 PIN 码Oct 04, 2023 pm 05:45 PM
解决方法:您的组织要求您更改 PIN 码Oct 04, 2023 pm 05:45 PM“你的组织要求你更改PIN消息”将显示在登录屏幕上。当在使用基于组织的帐户设置的电脑上达到PIN过期限制时,就会发生这种情况,在该电脑上,他们可以控制个人设备。但是,如果您使用个人帐户设置了Windows,则理想情况下不应显示错误消息。虽然情况并非总是如此。大多数遇到错误的用户使用个人帐户报告。为什么我的组织要求我在Windows11上更改我的PIN?可能是您的帐户与组织相关联,您的主要方法应该是验证这一点。联系域管理员会有所帮助!此外,配置错误的本地策略设置或不正确的注册表项也可能导致错误。即
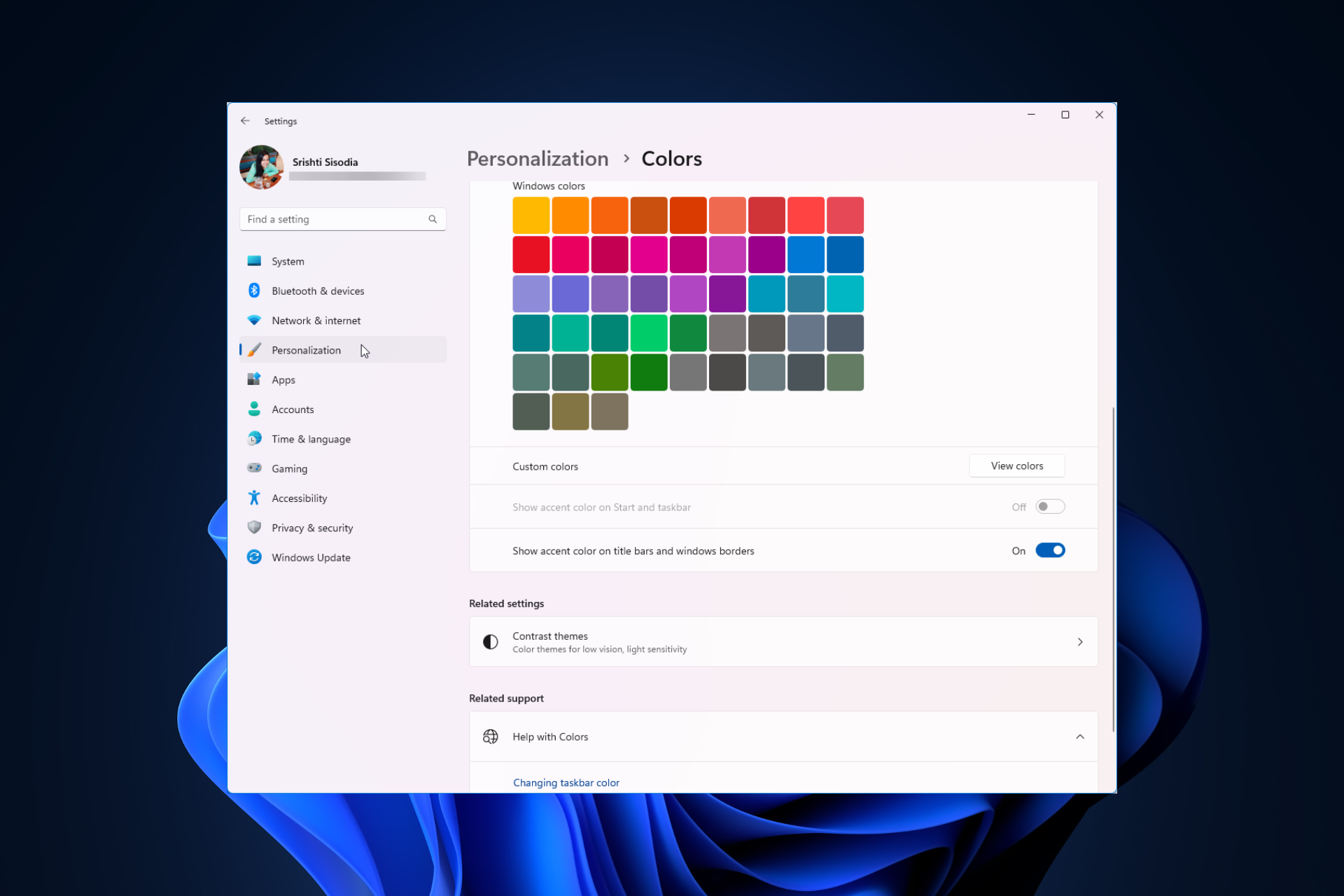 Windows 11 上调整窗口边框设置的方法:更改颜色和大小Sep 22, 2023 am 11:37 AM
Windows 11 上调整窗口边框设置的方法:更改颜色和大小Sep 22, 2023 am 11:37 AMWindows11将清新优雅的设计带到了最前沿;现代界面允许您个性化和更改最精细的细节,例如窗口边框。在本指南中,我们将讨论分步说明,以帮助您在Windows操作系统中创建反映您的风格的环境。如何更改窗口边框设置?按+打开“设置”应用。WindowsI转到个性化,然后单击颜色设置。颜色更改窗口边框设置窗口11“宽度=”643“高度=”500“>找到在标题栏和窗口边框上显示强调色选项,然后切换它旁边的开关。若要在“开始”菜单和任务栏上显示主题色,请打开“在开始”菜单和任务栏上显示主题
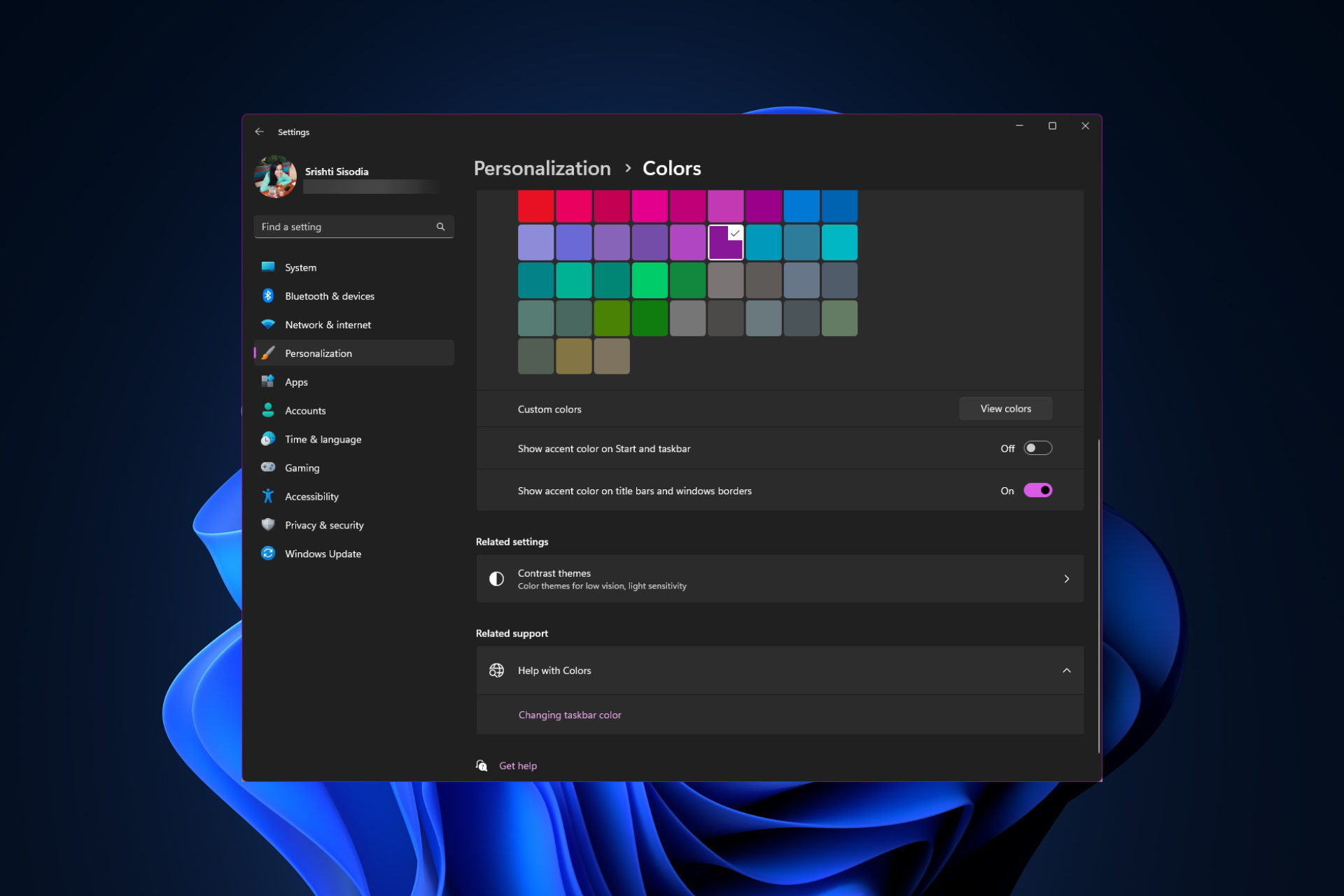 如何在 Windows 11 上更改标题栏颜色?Sep 14, 2023 pm 03:33 PM
如何在 Windows 11 上更改标题栏颜色?Sep 14, 2023 pm 03:33 PM默认情况下,Windows11上的标题栏颜色取决于您选择的深色/浅色主题。但是,您可以将其更改为所需的任何颜色。在本指南中,我们将讨论三种方法的分步说明,以更改它并个性化您的桌面体验,使其具有视觉吸引力。是否可以更改活动和非活动窗口的标题栏颜色?是的,您可以使用“设置”应用更改活动窗口的标题栏颜色,也可以使用注册表编辑器更改非活动窗口的标题栏颜色。若要了解这些步骤,请转到下一部分。如何在Windows11中更改标题栏的颜色?1.使用“设置”应用按+打开设置窗口。WindowsI前往“个性化”,然
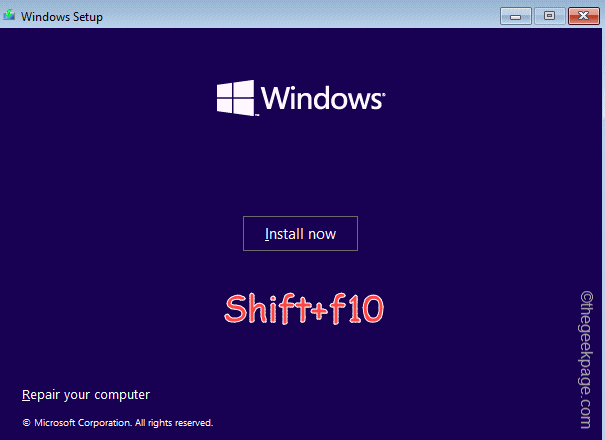 OOBELANGUAGE错误Windows 11 / 10修复中出现问题的问题Jul 16, 2023 pm 03:29 PM
OOBELANGUAGE错误Windows 11 / 10修复中出现问题的问题Jul 16, 2023 pm 03:29 PM您是否在Windows安装程序页面上看到“出现问题”以及“OOBELANGUAGE”语句?Windows的安装有时会因此类错误而停止。OOBE表示开箱即用的体验。正如错误提示所表示的那样,这是与OOBE语言选择相关的问题。没有什么可担心的,你可以通过OOBE屏幕本身的漂亮注册表编辑来解决这个问题。快速修复–1.单击OOBE应用底部的“重试”按钮。这将继续进行该过程,而不会再打嗝。2.使用电源按钮强制关闭系统。系统重新启动后,OOBE应继续。3.断开系统与互联网的连接。在脱机模式下完成OOBE的所
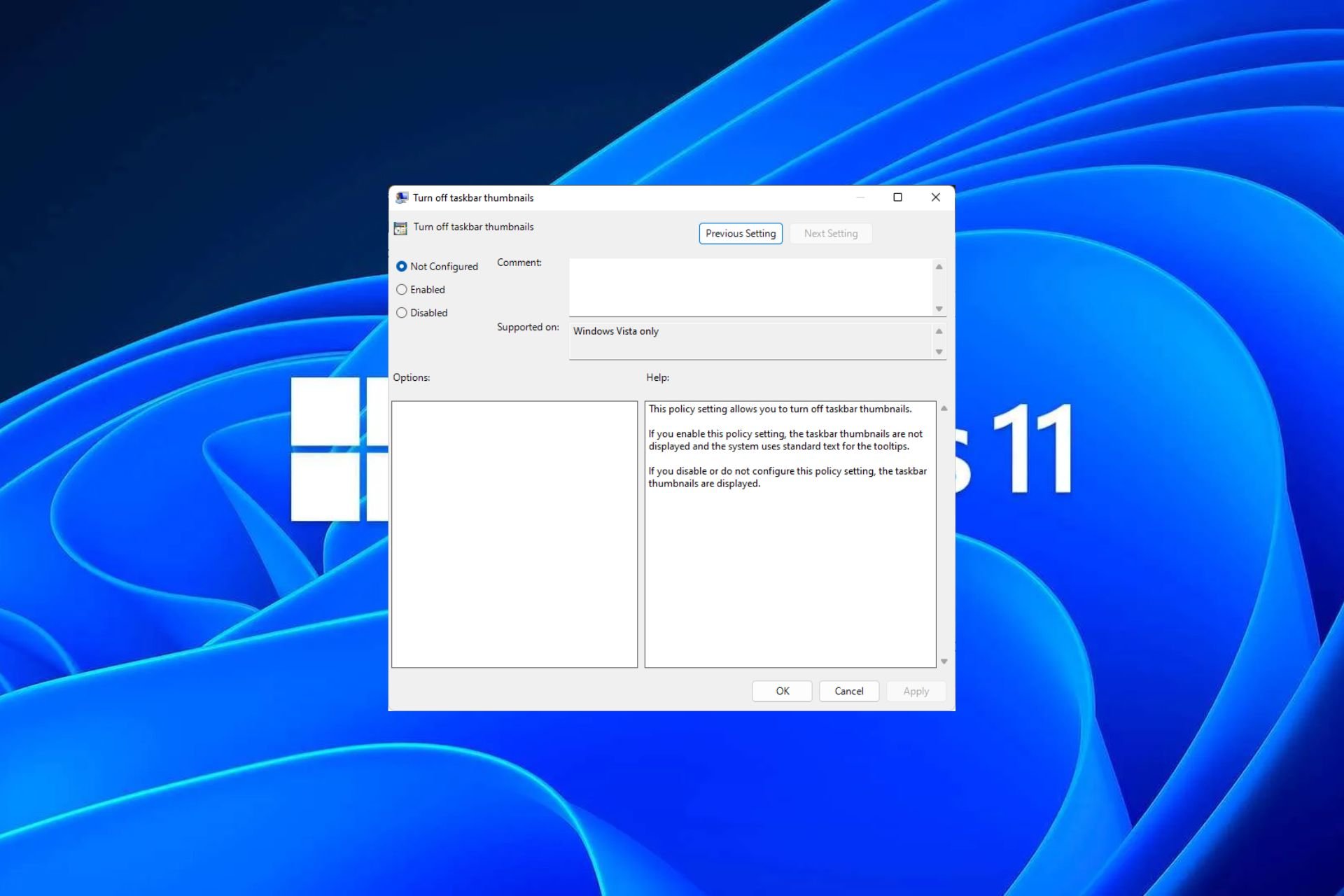 Windows 11 上启用或禁用任务栏缩略图预览的方法Sep 15, 2023 pm 03:57 PM
Windows 11 上启用或禁用任务栏缩略图预览的方法Sep 15, 2023 pm 03:57 PM任务栏缩略图可能很有趣,但它们也可能分散注意力或烦人。考虑到您将鼠标悬停在该区域的频率,您可能无意中关闭了重要窗口几次。另一个缺点是它使用更多的系统资源,因此,如果您一直在寻找一种提高资源效率的方法,我们将向您展示如何禁用它。不过,如果您的硬件规格可以处理它并且您喜欢预览版,则可以启用它。如何在Windows11中启用任务栏缩略图预览?1.使用“设置”应用点击键并单击设置。Windows单击系统,然后选择关于。点击高级系统设置。导航到“高级”选项卡,然后选择“性能”下的“设置”。在“视觉效果”选
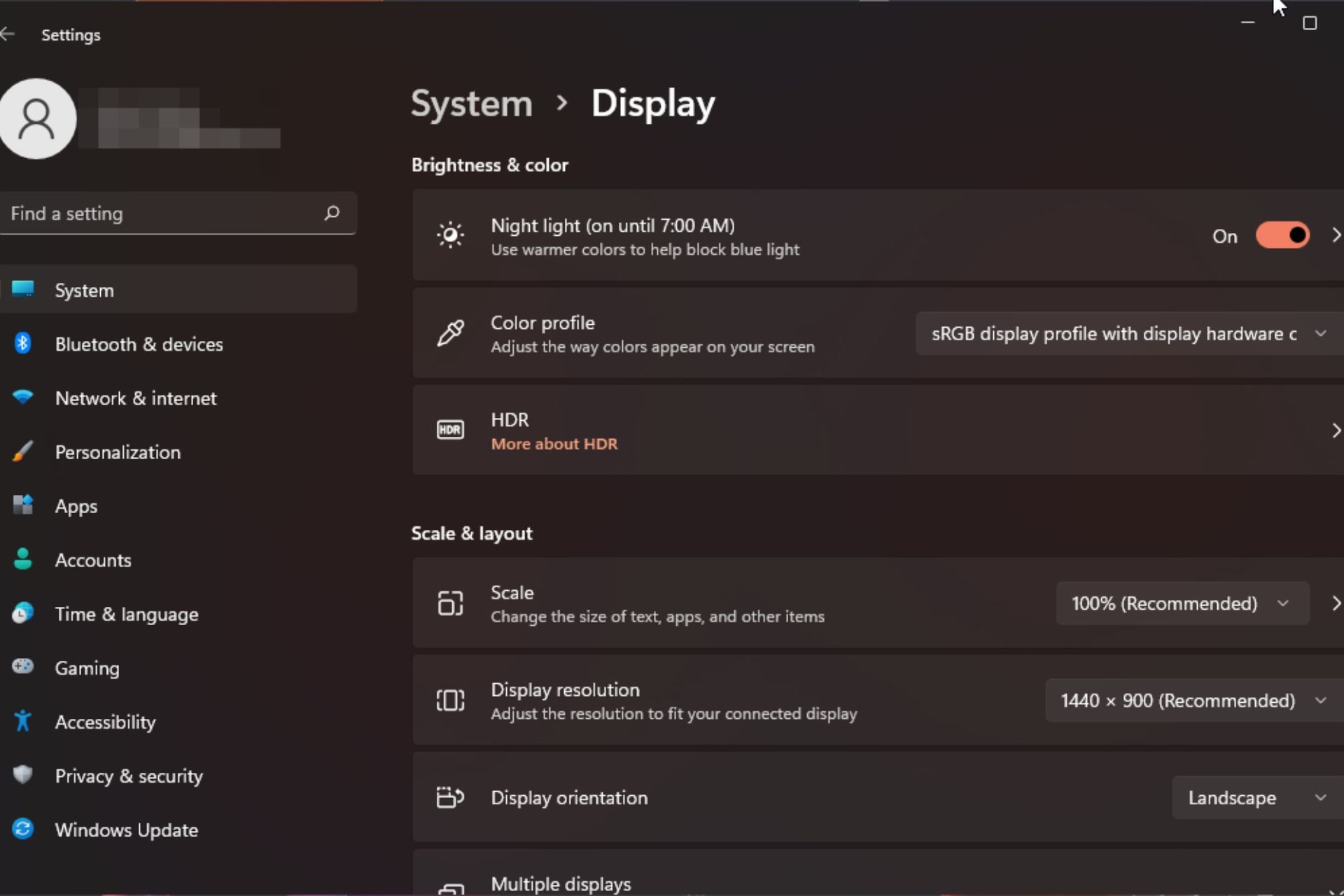 Windows 11 上的显示缩放比例调整指南Sep 19, 2023 pm 06:45 PM
Windows 11 上的显示缩放比例调整指南Sep 19, 2023 pm 06:45 PM在Windows11上的显示缩放方面,我们都有不同的偏好。有些人喜欢大图标,有些人喜欢小图标。但是,我们都同意拥有正确的缩放比例很重要。字体缩放不良或图像过度缩放可能是工作时真正的生产力杀手,因此您需要知道如何对其进行自定义以充分利用系统功能。自定义缩放的优点:对于难以阅读屏幕上的文本的人来说,这是一个有用的功能。它可以帮助您一次在屏幕上查看更多内容。您可以创建仅适用于某些监视器和应用程序的自定义扩展配置文件。可以帮助提高低端硬件的性能。它使您可以更好地控制屏幕上的内容。如何在Windows11
 10种在 Windows 11 上调整亮度的方法Dec 18, 2023 pm 02:21 PM
10种在 Windows 11 上调整亮度的方法Dec 18, 2023 pm 02:21 PM屏幕亮度是使用现代计算设备不可或缺的一部分,尤其是当您长时间注视屏幕时。它可以帮助您减轻眼睛疲劳,提高易读性,并轻松有效地查看内容。但是,根据您的设置,有时很难管理亮度,尤其是在具有新UI更改的Windows11上。如果您在调整亮度时遇到问题,以下是在Windows11上管理亮度的所有方法。如何在Windows11上更改亮度[10种方式解释]单显示器用户可以使用以下方法在Windows11上调整亮度。这包括使用单个显示器的台式机系统以及笔记本电脑。让我们开始吧。方法1:使用操作中心操作中心是访问
 如何在Safari中关闭iPhone的隐私浏览身份验证?Nov 29, 2023 pm 11:21 PM
如何在Safari中关闭iPhone的隐私浏览身份验证?Nov 29, 2023 pm 11:21 PM在iOS17中,Apple为其移动操作系统引入了几项新的隐私和安全功能,其中之一是能够要求对Safari中的隐私浏览选项卡进行二次身份验证。以下是它的工作原理以及如何将其关闭。在运行iOS17或iPadOS17的iPhone或iPad上,如果您在Safari浏览器中打开了任何“无痕浏览”标签页,然后退出会话或App,Apple的浏览器现在需要面容ID/触控ID认证或密码才能再次访问它们。换句话说,如果有人在解锁您的iPhone或iPad时拿到了它,他们仍然无法在不知道您的密码的情况下查看您的隐私


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

EditPlus Chinese cracked version
Small size, syntax highlighting, does not support code prompt function

SublimeText3 Linux new version
SublimeText3 Linux latest version

ZendStudio 13.5.1 Mac
Powerful PHP integrated development environment

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 English version
Recommended: Win version, supports code prompts!





