 Backend Development
Backend Development PHP Tutorial
PHP Tutorial Good book recommendation: 'Hacker's Tips: A Practical Guide to Penetration Testing'
Good book recommendation: 'Hacker's Tips: A Practical Guide to Penetration Testing'Introduction

So-called penetration testing is to use various vulnerability scanning tools to evaluate network security by simulating hacker attack methods.
This book uses a large number of real cases and philatelic help suggestions to explain some of the obstacles that will be faced during penetration testing, as well as the corresponding solutions. This book is divided into 10 chapters, which cover the installation and configuration of attack machines/tools involved in this book, network scanning, vulnerability exploitation, manually finding and searching for web application vulnerabilities, and how to obtain more important information after the system is compromised. Information, social engineering skills, physical access attacks, methods to circumvent anti-virus software, tips on cracking passwords and a summary of the final results.
This book is organized in an orderly manner, and the chapters are directly independent of each other. Readers can read on demand or read chapter by chapter. This book does not require readers to have a background in penetration testing, but it will be more helpful to understand the content of this book if they have relevant experience.
About the author
Peter Kim is the CEO and chairman of Secure Planet. He has nearly 10 years of experience in the security field and has been engaged in penetration testing for the past 7 years. He has taught penetration testing and network security courses at Howard Community College in Maryland and holds numerous security-related certifications.
Recommendation Index
The penetration testing book with the best reputation on the market. It has been ranked first on Amazon in the United States for a long time and has received rave reviews. The English version of the paper book sold 17,000 copies in one year, and the electronic version was sold. With 7,500 copies sold, it outsold all other similar penetration testing books.
Spoiler: Rugby
The book explains the tactics of penetration testing in rugby jargon. The content is as follows:
<span>1、赛前准备—安装:关于如何配置本书所用到的攻击机器、工具。 2、发球前—扫描网络:在出招之前,需要进行扫描,了解即将面对的环境。本章将深入探讨寻找目标信息、智能扫描的相关内容。 3、带球—漏洞利用:利用扫描中所发现的漏洞,对系统进行攻击。从现在开始我们就着手行动了。 4、抛传—Web应用程序的人工检测技术:有时,您需要发挥创意,寻找公开的目标。我们将会看看如何手动地寻找、攻击Web应用。 5、横传—渗透内网:攻陷一个系统后,如何通过网络获取更重要的信息。 6、助攻—社会工程学:通过表演来迷惑敌人,本章将解释一些社会工程学方面的技巧。 7、短传—需要物理访问的攻击:一个要求很近距离的漂亮短踢。这里将描述需要物理访问的攻击。 8、四分卫突破—规避反病毒检测:当您距离很近时,偷袭是很棒的。多数情况下,您会面临反病毒软件的阻挠。为解决这一阻碍,本章将介绍规避杀毒系统的方法。 9、特勤组—破解、利用和技巧:破解密码、漏洞利用,以及一些小技巧。 10、赛后—分析报告:比赛过程分析和成果汇报。 11、继续教育:与读者分享为提升渗透测试水平而有必要做的一些事情,如参加安全会议、参加培训课程、阅读相关图书、研究漏洞框架、参加CTF比赛等。<br></span>
The above introduces the recommendation of a good book: "Hacker's Tips: A Practical Guide to Penetration Testing", which includes various aspects. I hope it will be helpful to friends who are interested in PHP tutorials.
 Web Speech API开发者指南:它是什么以及如何工作Apr 11, 2023 pm 07:22 PM
Web Speech API开发者指南:它是什么以及如何工作Apr 11, 2023 pm 07:22 PM译者 | 李睿审校 | 孙淑娟Web Speech API是一种Web技术,允许用户将语音数据合并到应用程序中。它可以通过浏览器将语音转换为文本,反之亦然。Web Speech API于2012年由W3C社区引入。而在十年之后,这个API仍在开发中,这是因为浏览器兼容性有限。该API既支持短时输入片段,例如一个口头命令,也支持长时连续的输入。广泛的听写能力使它非常适合与Applause应用程序集成,而简短的输入很适合语言翻译。语音识别对可访问性产生了巨大的影响。残疾用户可以使用语音更轻松地浏览
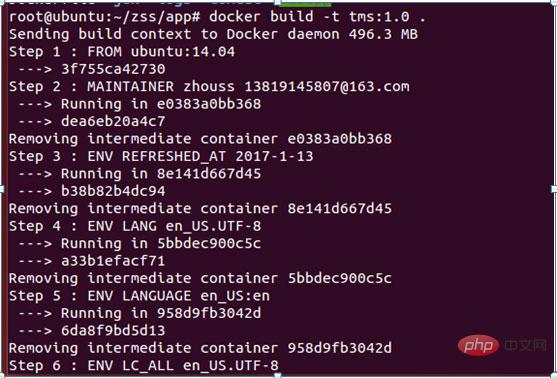 如何使用Docker部署Java Web应用程序Apr 25, 2023 pm 08:28 PM
如何使用Docker部署Java Web应用程序Apr 25, 2023 pm 08:28 PMdocker部署javaweb系统1.在root目录下创建一个路径test/appmkdirtest&&cdtest&&mkdirapp&&cdapp2.将apache-tomcat-7.0.29.tar.gz及jdk-7u25-linux-x64.tar.gz拷贝到app目录下3.解压两个tar.gz文件tar-zxvfapache-tomcat-7.0.29.tar.gztar-zxvfjdk-7u25-linux-x64.tar.gz4.对解
 web端是什么意思Apr 17, 2019 pm 04:01 PM
web端是什么意思Apr 17, 2019 pm 04:01 PMweb端指的是电脑端的网页版。在网页设计中我们称web为网页,它表现为三种形式,分别是超文本(hypertext)、超媒体(hypermedia)和超文本传输协议(HTTP)。
 web前端和后端开发有什么区别Jan 29, 2023 am 10:27 AM
web前端和后端开发有什么区别Jan 29, 2023 am 10:27 AM区别:1、前端指的是用户可见的界面,后端是指用户看不见的东西,考虑的是底层业务逻辑的实现,平台的稳定性与性能等。2、前端开发用到的技术包括html5、css3、js、jquery、Bootstrap、Node.js、Vue等;而后端开发用到的是java、php、Http协议等服务器技术。3、从应用范围来看,前端开发不仅被常人所知,且应用场景也要比后端广泛的太多太多。
 web前端打包工具有哪些Aug 23, 2022 pm 05:31 PM
web前端打包工具有哪些Aug 23, 2022 pm 05:31 PMweb前端打包工具有:1、Webpack,是一个模块化管理工具和打包工具可以将不同模块的文件打包整合在一起,并且保证它们之间的引用正确,执行有序;2、Grunt,一个前端打包构建工具;3、Gulp,用代码方式来写打包脚本;4、Rollup,ES6模块化打包工具;5、Parcel,一款速度极快、零配置的web应用程序打包器;6、equireJS,是一个JS文件和模块加载器。
 深入探讨“高并发大流量”访问的解决思路和方案May 11, 2022 pm 02:18 PM
深入探讨“高并发大流量”访问的解决思路和方案May 11, 2022 pm 02:18 PM怎么解决高并发大流量问题?下面本篇文章就来给大家分享下高并发大流量web解决思路及方案,希望对大家有所帮助!
 Python轻量级Web框架:Bottle库!Apr 13, 2023 pm 02:10 PM
Python轻量级Web框架:Bottle库!Apr 13, 2023 pm 02:10 PM和它本身的轻便一样,Bottle库的使用也十分简单。相信在看到本文前,读者对python也已经有了简单的了解。那么究竟何种神秘的操作,才能用百行代码完成一个服务器的功能?让我们拭目以待。1. Bottle库安装1)使用pip安装2)下载Bottle文件https://github.com/bottlepy/bottle/blob/master/bottle.py2.“HelloWorld!”所谓万事功成先HelloWorld,从这个简单的示例中,了解Bottle的基本机制。先上代码:首先我们从b
 web是前端还是后端Aug 24, 2022 pm 04:10 PM
web是前端还是后端Aug 24, 2022 pm 04:10 PMweb有前端,也有后端。web前端也被称为“客户端”,是关于用户可以看到和体验的网站的视觉方面,即用户所看到的一切Web浏览器展示的内容,涉及用户可以看到,触摸和体验的一切。web后端也称为“服务器端”,是用户在浏览器中无法查看和交互的所有内容,web后端负责存储和组织数据,并确保web前端的所有内容都能正常工作。web后端与前端通信,发送和接收信息以显示为网页。


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

SAP NetWeaver Server Adapter for Eclipse
Integrate Eclipse with SAP NetWeaver application server.

Atom editor mac version download
The most popular open source editor

mPDF
mPDF is a PHP library that can generate PDF files from UTF-8 encoded HTML. The original author, Ian Back, wrote mPDF to output PDF files "on the fly" from his website and handle different languages. It is slower than original scripts like HTML2FPDF and produces larger files when using Unicode fonts, but supports CSS styles etc. and has a lot of enhancements. Supports almost all languages, including RTL (Arabic and Hebrew) and CJK (Chinese, Japanese and Korean). Supports nested block-level elements (such as P, DIV),

SecLists
SecLists is the ultimate security tester's companion. It is a collection of various types of lists that are frequently used during security assessments, all in one place. SecLists helps make security testing more efficient and productive by conveniently providing all the lists a security tester might need. List types include usernames, passwords, URLs, fuzzing payloads, sensitive data patterns, web shells, and more. The tester can simply pull this repository onto a new test machine and he will have access to every type of list he needs.





