How to achieve the goal:
How to avoid repeated submissions?
Save an array in the SESSION. This array stores the successfully submitted tokens. During background processing, first determine whether the token is in this array. If it exists, indicate that it is Repeat submission.
How to check the source?
Optional, when this token is generated, the current session_id is added. If someone else copies your html (token copy), when submitting, theoretically the session_id contained in the token will be If it is not equal to the current session_id, you can judge that this submission is an external submission.
How to match the action to be executed?
When tokenizing, you need to write the action name of this token into the token, so that when processing, Just solve this action and compare it.
The GToken I wrote before could not meet the second point mentioned above. I modified it today and added function 2. Personally, I think it is okay.
Please look at the code and see where it feels. If there is anything unreasonable, please let me know! Thank you.
I found a method online for encryption and made some modifications.
GEncrypt.inc.php:
Copy the code The code is as follows:
Copy the code The code is as follows:
The above introduces the PHP Token design of www.stocke.com.cn, including the content of www.stocke.com.cn. I hope it will be helpful to friends who are interested in PHP tutorials.
class GEncrypt extends GSuperclass {
protected static function keyED($txt,$encrypt_key){
$encrypt_key = md5($encrypt_key);
$ctr=0;
$tmp = ""; i=0;$i
$tmp.= substr($txt,$i,1) ^ substr($encrypt_key,$ctr,1); t,$key){
32000));
$encrypt_key = md5(((float) date("YmdHis") + rand(10000000000000000,99999999999999999)).rand(100000,999999));
$ctr=0;
$tmp = ""; For ($ i = 0; $ i & lt; strlen ($ txt); $ i ++) {
IF ($ ctr == Strlen ($ Encrypt_Key)) $ ctr = 0; ctr,1) . (substr($txt,$i,1) ^ substr($encrypt_key,$ctr,1)); $key) );
}
public static function decrypt($txt,$key){
$txt = self::keyED( base64_decode($txt),$key);
$tmp = ""; for ($i=0 ;$i
Method:
a, granteToken Parameters: formName, which is the action name, key is the encryption/decryption key.
Returns a string in the form: encryption (formName: session_id)
b, isToken Parameters: token is the result generated by grantToken, formName, action name, whether fromCheck checks the source, and if it is true, it also determines whether the session_id in the token is the same as the current session_id.
c, dropToken, when an action is successfully executed, call this Function, record this token into the session,
/**
* Principle: When requesting to allocate a token, find a way to allocate a unique token, base64( time + rand + action)
* If submitted, record this token, indicating that this token has been used before, and you can follow it to avoid duplication submit.
*
*/
class GToken {
/**
* Get all the current tokens */
public static function getTokens(){
$tokens = $_SESSION[GConfig::SESSION_KEY_TOKEN ];
if (empty($tokens) && !is_array($tokens)) {
$tokens = array();
}
return $tokens;
}
/**
* Generate a new Token */
public static function granteToken($formName,$key = GConfig::ENCRYPT_KEY ){
$token = GEncrypt::encrypt($formName.":".session_id(),$key);
return $token;
}
/**
* Deleting a token actually adds an element to an array in the session, indicating that the token has been used before to avoid repeated submission of data.
* */
public static function dropToken($token){
$tokens = self::getTokens();
$tokens[] = $token;
GSession::set(GConfig::SESSION_KEY_TOKEN ,$tokens);
}
/**
medium additional Whether the session_id is the same as the current session_id.
* @param string $key encryption key
* @return boolean
*/
public static function isToken($token,$formName,$fromCheck = false,$key = GConfig::ENCRYPT_KEY){
$tokens = self::getTokens();
if (in_array($token,$tokens)) //如果存在,说明是以使用过的token
return false;
$source = split(":", GEncrypt::decrypt($token,$key));
if($fromCheck)
return $source[1] == session_id() && $source[0] == $formName;
else
return $source[0] == $formName;
}
}
?>
Example:
First take out the token from $_POST and use isToken to judge.  Downloading this file seems to be no problem.
Downloading this file seems to be no problem.
If you want to judge whether it is a matching action, you can change the formName in isToken. Running, very good, no matching. Prove this success.
Whether it can avoid repeated submission, I have not verified, it is too simple logic.
The rest is to judge whether the source check is working normally.
Generate the above example html copy to a local web page (to achieve the purpose of different domains), run, check the source is unknown, and no action is performed (the third parameter of isToken needs to be set to true).
Set the third parameter of isToken Set it to false, submit, and the specified action is executed!
Okay, so far, I don’t know if there are still BUGs somewhere, which will need to be debugged and modified slowly in long-term use!
 11 Best PHP URL Shortener Scripts (Free and Premium)Mar 03, 2025 am 10:49 AM
11 Best PHP URL Shortener Scripts (Free and Premium)Mar 03, 2025 am 10:49 AMLong URLs, often cluttered with keywords and tracking parameters, can deter visitors. A URL shortening script offers a solution, creating concise links ideal for social media and other platforms. These scripts are valuable for individual websites a
 Introduction to the Instagram APIMar 02, 2025 am 09:32 AM
Introduction to the Instagram APIMar 02, 2025 am 09:32 AMFollowing its high-profile acquisition by Facebook in 2012, Instagram adopted two sets of APIs for third-party use. These are the Instagram Graph API and the Instagram Basic Display API.As a developer building an app that requires information from a
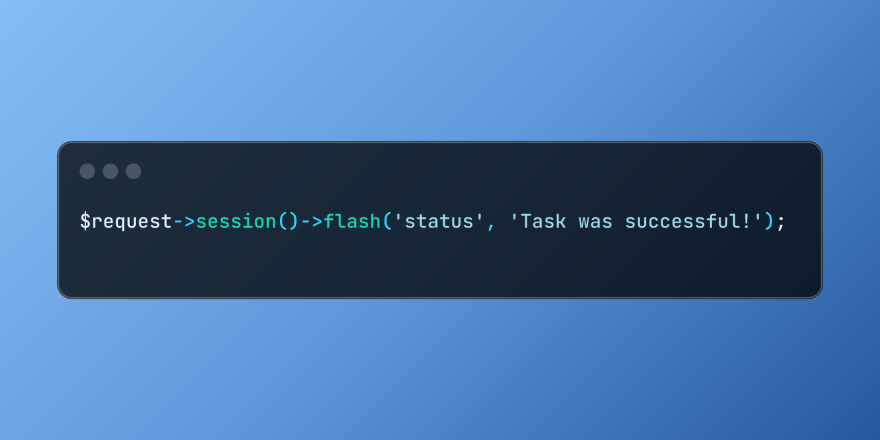 Working with Flash Session Data in LaravelMar 12, 2025 pm 05:08 PM
Working with Flash Session Data in LaravelMar 12, 2025 pm 05:08 PMLaravel simplifies handling temporary session data using its intuitive flash methods. This is perfect for displaying brief messages, alerts, or notifications within your application. Data persists only for the subsequent request by default: $request-
 Build a React App With a Laravel Back End: Part 2, ReactMar 04, 2025 am 09:33 AM
Build a React App With a Laravel Back End: Part 2, ReactMar 04, 2025 am 09:33 AMThis is the second and final part of the series on building a React application with a Laravel back-end. In the first part of the series, we created a RESTful API using Laravel for a basic product-listing application. In this tutorial, we will be dev
 Simplified HTTP Response Mocking in Laravel TestsMar 12, 2025 pm 05:09 PM
Simplified HTTP Response Mocking in Laravel TestsMar 12, 2025 pm 05:09 PMLaravel provides concise HTTP response simulation syntax, simplifying HTTP interaction testing. This approach significantly reduces code redundancy while making your test simulation more intuitive. The basic implementation provides a variety of response type shortcuts: use Illuminate\Support\Facades\Http; Http::fake([ 'google.com' => 'Hello World', 'github.com' => ['foo' => 'bar'], 'forge.laravel.com' =>
 cURL in PHP: How to Use the PHP cURL Extension in REST APIsMar 14, 2025 am 11:42 AM
cURL in PHP: How to Use the PHP cURL Extension in REST APIsMar 14, 2025 am 11:42 AMThe PHP Client URL (cURL) extension is a powerful tool for developers, enabling seamless interaction with remote servers and REST APIs. By leveraging libcurl, a well-respected multi-protocol file transfer library, PHP cURL facilitates efficient execution of various network protocols, including HTTP, HTTPS, and FTP. This extension offers granular control over HTTP requests, supports multiple concurrent operations, and provides built-in security features.
 12 Best PHP Chat Scripts on CodeCanyonMar 13, 2025 pm 12:08 PM
12 Best PHP Chat Scripts on CodeCanyonMar 13, 2025 pm 12:08 PMDo you want to provide real-time, instant solutions to your customers' most pressing problems? Live chat lets you have real-time conversations with customers and resolve their problems instantly. It allows you to provide faster service to your custom
 Announcement of 2025 PHP Situation SurveyMar 03, 2025 pm 04:20 PM
Announcement of 2025 PHP Situation SurveyMar 03, 2025 pm 04:20 PMThe 2025 PHP Landscape Survey investigates current PHP development trends. It explores framework usage, deployment methods, and challenges, aiming to provide insights for developers and businesses. The survey anticipates growth in modern PHP versio


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Dreamweaver CS6
Visual web development tools

SecLists
SecLists is the ultimate security tester's companion. It is a collection of various types of lists that are frequently used during security assessments, all in one place. SecLists helps make security testing more efficient and productive by conveniently providing all the lists a security tester might need. List types include usernames, passwords, URLs, fuzzing payloads, sensitive data patterns, web shells, and more. The tester can simply pull this repository onto a new test machine and he will have access to every type of list he needs.

MantisBT
Mantis is an easy-to-deploy web-based defect tracking tool designed to aid in product defect tracking. It requires PHP, MySQL and a web server. Check out our demo and hosting services.

mPDF
mPDF is a PHP library that can generate PDF files from UTF-8 encoded HTML. The original author, Ian Back, wrote mPDF to output PDF files "on the fly" from his website and handle different languages. It is slower than original scripts like HTML2FPDF and produces larger files when using Unicode fonts, but supports CSS styles etc. and has a lot of enhancements. Supports almost all languages, including RTL (Arabic and Hebrew) and CJK (Chinese, Japanese and Korean). Supports nested block-level elements (such as P, DIV),

ZendStudio 13.5.1 Mac
Powerful PHP integrated development environment






