|
The operational security of the website is definitely an issue that every webmaster must consider. As we all know, most hackers attack websites by using SQL injection. This is what we often say why? The most original static website is the safest. Today we will talk about the security specifications of PHP injection to prevent your website from being injected by SQL. Nowadays, the mainstream website development language is still PHP, so let’s start with how to prevent SQL injection on PHP websites: Security Prevention of Php Injection Through the above process, we can understand the principles and techniques of php injection. Of course, we can also develop corresponding prevention methods: The first is the security settings of the server. Here are mainly the security settings of php+mysql and the security settings of the Linux host. To prevent php+mysql injection, first set magic_quotes_gpc to On and display_errs to Off. If it is an id type, we use intval() to convert it into an integer type, as shown in the code: $idintval($id); mysql_query”*fromexamplewherearticieid’$id’”; Or write like this: mysql_query(”SELECT*FROMarticleWHEREarticleid”.intval($id).””) If it is a character type, use addslashes() to filter it, and then filter "%" and "_", such as: $searchaddslashes($search); $searchstr_replace(“_”,”_”,$search); $searchstr_replace(“%”,”%”,$search); Of course, you can also add PHP universal anti-injection code: /***************************** PHP universal anti-injection security code Description: Determine whether the passed variable contains illegal characters Such as $_POST, $_GET Function: Anti-injection
Then add include("checkpostget.php"); before each php file ****************************/ In addition, the administrator username and password are md5 encrypted, which can effectively prevent PHP injection. There are also some security precautions that need to be strengthened on the server and mysql. For security settings of linux server: To encrypt the password, use the "/usr/sbin/authconfig" tool to turn on the password shadow function and encrypt passwd. To prohibit access to important files, enter the Linux command interface and enter at the prompt: #chmod600/etc/inetd.conf//Change the file attributes to 600 #chattr+I /etc/inetd.conf // Ensure that the file owner is root #chattr–I /etc/inetd.conf //Restrict changes to this file It is forbidden for any user to change to the root user through the su command Add the following two lines at the beginning of the su configuration file, that is, the /etc/pam.d/ directory: Auth sufficient /lib/security/pam_rootok.sodebug Auth required /lib/security/pam_whell.sogroupwheel Delete all special accounts #userdel lp etc. Delete user #groupdellpetc delete group Ban unused suid/sgid programs #find/-typef(-perm-04000 -o–perm-02000)-execls–lg{}; http://hi.baidu.com/bigideaer/bl... 7e76e11a4cffd0.html To determine whether the passed variables contain illegal characters, we put the following code into a public file, such as security.inc.php. Include this file in each file, then all the files submitted to any program can be After the variables are filtered, we achieve the effect once and for all. Brief description: /*************************** Description: Determine whether the passed variable contains illegal characters Such as $_POST, $_GET Function: Anti-injection **************************/ The code is as follows:
Method 2 The code is as follows:
The second method is written in a separate file and imported into every PHP file Then you can escape every data functionsaddslashes($string){ if(is_array($string)){ feach($stringas$key>$val){ $string[$key]saddslashes($val); } }else{ $stringaddslashes($string); } return$string; } ################################################ ############### $magic_quoteget_magic_quotes_gpc(); if(empty($magic_quote)){ $_GETsaddslashes($_GET); $_POSTsaddslashes($_POST); } |
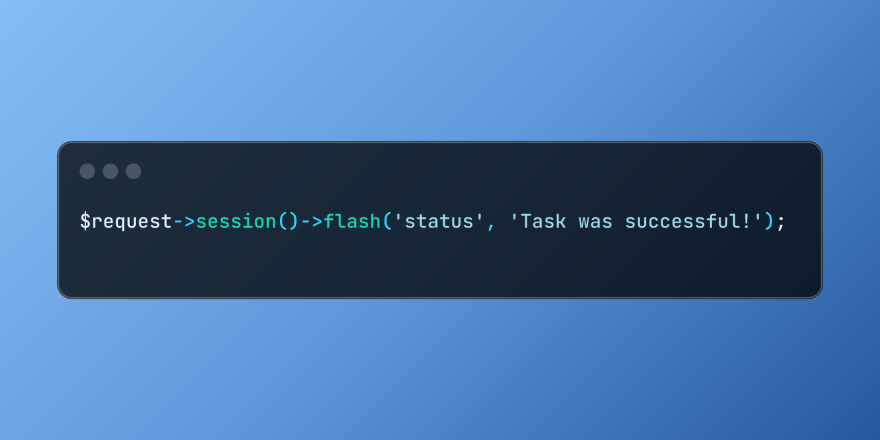 Working with Flash Session Data in LaravelMar 12, 2025 pm 05:08 PM
Working with Flash Session Data in LaravelMar 12, 2025 pm 05:08 PMLaravel simplifies handling temporary session data using its intuitive flash methods. This is perfect for displaying brief messages, alerts, or notifications within your application. Data persists only for the subsequent request by default: $request-
 cURL in PHP: How to Use the PHP cURL Extension in REST APIsMar 14, 2025 am 11:42 AM
cURL in PHP: How to Use the PHP cURL Extension in REST APIsMar 14, 2025 am 11:42 AMThe PHP Client URL (cURL) extension is a powerful tool for developers, enabling seamless interaction with remote servers and REST APIs. By leveraging libcurl, a well-respected multi-protocol file transfer library, PHP cURL facilitates efficient execution of various network protocols, including HTTP, HTTPS, and FTP. This extension offers granular control over HTTP requests, supports multiple concurrent operations, and provides built-in security features.
 Simplified HTTP Response Mocking in Laravel TestsMar 12, 2025 pm 05:09 PM
Simplified HTTP Response Mocking in Laravel TestsMar 12, 2025 pm 05:09 PMLaravel provides concise HTTP response simulation syntax, simplifying HTTP interaction testing. This approach significantly reduces code redundancy while making your test simulation more intuitive. The basic implementation provides a variety of response type shortcuts: use Illuminate\Support\Facades\Http; Http::fake([ 'google.com' => 'Hello World', 'github.com' => ['foo' => 'bar'], 'forge.laravel.com' =>
 12 Best PHP Chat Scripts on CodeCanyonMar 13, 2025 pm 12:08 PM
12 Best PHP Chat Scripts on CodeCanyonMar 13, 2025 pm 12:08 PMDo you want to provide real-time, instant solutions to your customers' most pressing problems? Live chat lets you have real-time conversations with customers and resolve their problems instantly. It allows you to provide faster service to your custom
 Explain the concept of late static binding in PHP.Mar 21, 2025 pm 01:33 PM
Explain the concept of late static binding in PHP.Mar 21, 2025 pm 01:33 PMArticle discusses late static binding (LSB) in PHP, introduced in PHP 5.3, allowing runtime resolution of static method calls for more flexible inheritance.Main issue: LSB vs. traditional polymorphism; LSB's practical applications and potential perfo
 How to Register and Use Laravel Service ProvidersMar 07, 2025 am 01:18 AM
How to Register and Use Laravel Service ProvidersMar 07, 2025 am 01:18 AMLaravel's service container and service providers are fundamental to its architecture. This article explores service containers, details service provider creation, registration, and demonstrates practical usage with examples. We'll begin with an ove
 PHP Logging: Best Practices for PHP Log AnalysisMar 10, 2025 pm 02:32 PM
PHP Logging: Best Practices for PHP Log AnalysisMar 10, 2025 pm 02:32 PMPHP logging is essential for monitoring and debugging web applications, as well as capturing critical events, errors, and runtime behavior. It provides valuable insights into system performance, helps identify issues, and supports faster troubleshoot
 Customizing/Extending Frameworks: How to add custom functionality.Mar 28, 2025 pm 05:12 PM
Customizing/Extending Frameworks: How to add custom functionality.Mar 28, 2025 pm 05:12 PMThe article discusses adding custom functionality to frameworks, focusing on understanding architecture, identifying extension points, and best practices for integration and debugging.


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

EditPlus Chinese cracked version
Small size, syntax highlighting, does not support code prompt function

ZendStudio 13.5.1 Mac
Powerful PHP integrated development environment

Safe Exam Browser
Safe Exam Browser is a secure browser environment for taking online exams securely. This software turns any computer into a secure workstation. It controls access to any utility and prevents students from using unauthorized resources.

Dreamweaver Mac version
Visual web development tools

VSCode Windows 64-bit Download
A free and powerful IDE editor launched by Microsoft






