1. addslashes
addslashes escapes special characters in SQL statements, including ('), (“), (), (NUL) four characters, This function is used when the DBMS does not have its own escape function, but if the DBMS has its own escape function, it is recommended to use the original function. For example, MySQL has the mysql_real_escape_string function to escape SQL. Note that before PHP5.3, magic_quotes_gpc was the default. When enabled, it mainly performs addslashes operations on $GET, $POST, and $COOKIE, so there is no need to repeatedly call addslashes on these variables, otherwise it will double escaping. However, magic_quotes_gpc has been abandoned in PHP5.3 and has been in use since PHP5. .4 has been removed. If you use the latest version of PHP, you don’t have to worry about this problem. stripslashes is the unescape function of addslashes.
2. htmlspecialchars
htmlspecialchars. Escape several special characters in HTML into HTML Entity (format: &xxxx;), including (&), ('), ("), () five characters.
& (AND) => > > > (greater than sign) => >
htmlspecialchars can be used to filter $GET, $POST, $COOKIE data to prevent XSS. Note that the htmlspecialchars function only escapes HTML characters that are considered to have security risks. If you want to escape all characters that can be escaped in HTML, please use htmlentities. htmlspecialchars_decode is the decode function of htmlspecialchars.
3. htmlentities
htmlentities escapes the escapable content in HTML into HTML Entity. html_entity_decode is the decode function of htmlentities.
4. mysql_real_escape_string
mysql_real_escape_string will call the MySQL library function mysql_real_escape_string, for (x00), (n), (r), (), ('), (x1a) Escape, that is, add a backslash () in front to prevent SQL injection. Note that you do not need to call stripslashes to unescape when reading the database data, because these backslashes are added when the database executes SQL, and the backslashes will be removed when the data is written to the database, so The content written to the database is the original data, and there will be no backslashes in front.
5. strip_tags
strip_tags will filter out NUL, HTML and PHP tags.
6. Conclusion
PHP’s own security functions cannot completely avoid XSS. It is recommended to use HTML Purifier
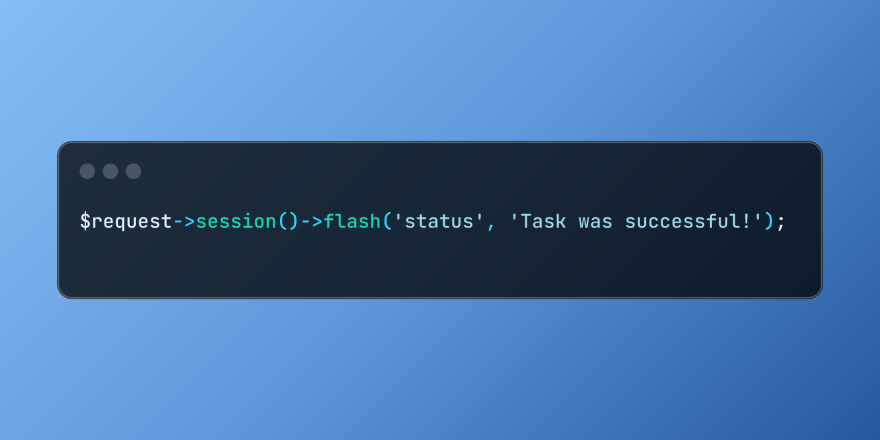 Working with Flash Session Data in LaravelMar 12, 2025 pm 05:08 PM
Working with Flash Session Data in LaravelMar 12, 2025 pm 05:08 PMLaravel simplifies handling temporary session data using its intuitive flash methods. This is perfect for displaying brief messages, alerts, or notifications within your application. Data persists only for the subsequent request by default: $request-
 cURL in PHP: How to Use the PHP cURL Extension in REST APIsMar 14, 2025 am 11:42 AM
cURL in PHP: How to Use the PHP cURL Extension in REST APIsMar 14, 2025 am 11:42 AMThe PHP Client URL (cURL) extension is a powerful tool for developers, enabling seamless interaction with remote servers and REST APIs. By leveraging libcurl, a well-respected multi-protocol file transfer library, PHP cURL facilitates efficient execution of various network protocols, including HTTP, HTTPS, and FTP. This extension offers granular control over HTTP requests, supports multiple concurrent operations, and provides built-in security features.
 Simplified HTTP Response Mocking in Laravel TestsMar 12, 2025 pm 05:09 PM
Simplified HTTP Response Mocking in Laravel TestsMar 12, 2025 pm 05:09 PMLaravel provides concise HTTP response simulation syntax, simplifying HTTP interaction testing. This approach significantly reduces code redundancy while making your test simulation more intuitive. The basic implementation provides a variety of response type shortcuts: use Illuminate\Support\Facades\Http; Http::fake([ 'google.com' => 'Hello World', 'github.com' => ['foo' => 'bar'], 'forge.laravel.com' =>
 How to Register and Use Laravel Service ProvidersMar 07, 2025 am 01:18 AM
How to Register and Use Laravel Service ProvidersMar 07, 2025 am 01:18 AMLaravel's service container and service providers are fundamental to its architecture. This article explores service containers, details service provider creation, registration, and demonstrates practical usage with examples. We'll begin with an ove
 12 Best PHP Chat Scripts on CodeCanyonMar 13, 2025 pm 12:08 PM
12 Best PHP Chat Scripts on CodeCanyonMar 13, 2025 pm 12:08 PMDo you want to provide real-time, instant solutions to your customers' most pressing problems? Live chat lets you have real-time conversations with customers and resolve their problems instantly. It allows you to provide faster service to your custom
 PHP Logging: Best Practices for PHP Log AnalysisMar 10, 2025 pm 02:32 PM
PHP Logging: Best Practices for PHP Log AnalysisMar 10, 2025 pm 02:32 PMPHP logging is essential for monitoring and debugging web applications, as well as capturing critical events, errors, and runtime behavior. It provides valuable insights into system performance, helps identify issues, and supports faster troubleshoot
 Explain the concept of late static binding in PHP.Mar 21, 2025 pm 01:33 PM
Explain the concept of late static binding in PHP.Mar 21, 2025 pm 01:33 PMArticle discusses late static binding (LSB) in PHP, introduced in PHP 5.3, allowing runtime resolution of static method calls for more flexible inheritance.Main issue: LSB vs. traditional polymorphism; LSB's practical applications and potential perfo
 Customizing/Extending Frameworks: How to add custom functionality.Mar 28, 2025 pm 05:12 PM
Customizing/Extending Frameworks: How to add custom functionality.Mar 28, 2025 pm 05:12 PMThe article discusses adding custom functionality to frameworks, focusing on understanding architecture, identifying extension points, and best practices for integration and debugging.


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

SAP NetWeaver Server Adapter for Eclipse
Integrate Eclipse with SAP NetWeaver application server.

Dreamweaver Mac version
Visual web development tools

SecLists
SecLists is the ultimate security tester's companion. It is a collection of various types of lists that are frequently used during security assessments, all in one place. SecLists helps make security testing more efficient and productive by conveniently providing all the lists a security tester might need. List types include usernames, passwords, URLs, fuzzing payloads, sensitive data patterns, web shells, and more. The tester can simply pull this repository onto a new test machine and he will have access to every type of list he needs.

SublimeText3 Linux new version
SublimeText3 Linux latest version

EditPlus Chinese cracked version
Small size, syntax highlighting, does not support code prompt function





