Cryptovirus malware spreads using various methods, but most of the techniques involve malicious files and data that are dangerous. The threat can inject a payload of the ransomware into the cracked game, or licensed version of the software package. These infections can happen quickly because the file is only needed to be launched on the machine.
Byya ransomware virus is affecting commonly used files like documents, images, audio, or video files, but this is the only symptom that is easily noticeable. Another issue is _readme.txt which appears placed on the desktop and in folders with locked data.
The ransom note informs users of what happened and states that the payment is the only good option for the file recovery. The sum of the ransom is $980, but these criminals rely on the discount offer to keep users scared and willing to pay up. DO NOT even contact these people behind the infection because the Byya file virus is developed by serious criminals that do not care about you. There are alternate options for this.

1. Check the decryption option
Djvu ransomware family that this Byya ransomware is coming from can be considered one of the most dangerous threats right now. The threat is known since 2018, but these last few years were a huge time for the threat actor group. Versions of the infection get released three or four at a time weekly.
These newer variants have been improved and advanced to the point where these versions, like the Byya file virus, are not decryptable because of the usage of the online IDs during the encryption process. The key is needed in the decryption process later on and the offline keys mean that they are formed before the versions are released and are the same for all victims.
The online IDs, on the other hand, are unique and formed when the C&C server[1] is connected during the encryption procedures. These are particular for each device, even when affected by the same Byya ransomware virus, for example. This is why decryption is not possible because to obtain the key decryption tool is requiring you need to pay or shut down the ransomware operations. Nevertheless, the previously created tools can sometimes work to this day.
- Download the app on official Emsisoft website.
- Once decrypt_STOPDjvu.exe shows up – click it.
- Follow the steps on the screen.
- The tool should locate the affected folders.

- You can also do it by pressing Add folder at the bottom.
- Press Decrypt.

- There are particular results that can occur indicating if the decryption is possible.
2. Remove the active virus
Ransomware can be hidden in various places on the machine, so its removal is difficult. However, this is the first step in the process of stopping a threat like this. Security tools and other programs can be disabled by an application like this, so the Byya ransomware is not easily detected on the machine.
Nevertheless, there are tools like anti-malware tools and programs that can find[2] these files and other threats like malware[3] or trojans that affect the machine further. The full system scan can locate malicious or potentially dangerous pieces and stop the active virus completely.
3. Restore affected system data
System issues are related to the particular damaged data in system folders. These threats like ransomware can access system data and other files that create problems with performance, programs, and other functions. Windows data got damaged and altered to keep the threat persistent.
DLL files, security programs, file recovery functions, and features can be corrupted, so people do not have options for the Byya file virus removal and file recovery procedures. These issues need to be solved and damage is taken care of to keep the computer running smoothly.
- Install FortectMac Washing Machine X9.
- Run the full system scan and wait for the complete analysis.
- Follow the on-screen steps.
- Allow the machine to get checked.
- Check the Summary.

- You can fix issues manually from the list.
- Purchasing a licensed version can help repair serious issues.
4. Recover files
- Get a tool like Data Recovery Pro from a trustworthy source.
- Follow installation instructions.
- Once that is finished, use the application.
- Select Everything or pick individual folders to recover.
- Press Next.
- Enable Deep scan at the bottom.

- Pick which Disk you want to be scanned.
- Scan.
- Hit Recover to restore files.

The above is the detailed content of How to recover .byya files?. For more information, please follow other related articles on the PHP Chinese website!
 Schedule 1 Dealer Not Working, See a Pro Guide with Top 7 FixesApr 14, 2025 pm 08:09 PM
Schedule 1 Dealer Not Working, See a Pro Guide with Top 7 FixesApr 14, 2025 pm 08:09 PMTroubleshooting Schedule 1 Dealer Issues: A Comprehensive Guide A malfunctioning Schedule 1 dealer can be incredibly frustrating. This guide provides multiple solutions to get your drug empire back on track. Schedule 1 Dealer Not Selling: The Problem
 Alert: Do Not Delete the New inetpub Folder in Windows 11Apr 14, 2025 pm 08:08 PM
Alert: Do Not Delete the New inetpub Folder in Windows 11Apr 14, 2025 pm 08:08 PMWindows 11 KB5055523 Update and the Mysterious inetpub Folder: Should You Worry? After installing the April 2025 Patch Tuesday update (KB5055523) on your Windows 11 (version 24H2) system, did a new inetpub folder suddenly appear on your C: drive? Th
 Discord Loading Chunk Failed: Fix with 4 Useful WaysApr 14, 2025 pm 08:03 PM
Discord Loading Chunk Failed: Fix with 4 Useful WaysApr 14, 2025 pm 08:03 PMDiscord Loading Scramble Error: Four Practical Solutions Discord loading failure issues plagued many users. This article will provide four effective solutions to help you quickly get rid of this problem! Method 1: Refresh Discord Simple refresh operations can often solve some minor problems. On the stuck interface, press Ctrl R (Windows) or CMD R (Mac) to refresh Discord and try to reconnect to the server. If it does not work, try the following method. Method 2: Task Manager ends the Discord process If Discord is completely unresponsive, force the relevant process to end: Step 1: Press Ct
 5 Useful Methods to Fix File Unreadable Google DriveApr 14, 2025 pm 08:02 PM
5 Useful Methods to Fix File Unreadable Google DriveApr 14, 2025 pm 08:02 PMThis guide tackles the frustrating "file unreadable Google Drive" error. We'll explore potential causes and offer six practical solutions. Quick Navigation: Fix 1: Internet Connection Check Fix 2: Google Drive Server Status Fix 3: File Si
 Fixes for SFC.DLL Is Either Not Designed to Run on WindowsApr 14, 2025 pm 08:01 PM
Fixes for SFC.DLL Is Either Not Designed to Run on WindowsApr 14, 2025 pm 08:01 PMEncountering the error "SFC.DLL is either not designed to run on Windows"? This guide provides solutions to resolve this frustrating issue, which often appears after startup or when launching specific programs. Quick Navigation: Understand
 How to fix KB5055613 fails to install in Windows 11?Apr 14, 2025 pm 08:00 PM
How to fix KB5055613 fails to install in Windows 11?Apr 14, 2025 pm 08:00 PMThe KB5055613 update, which was a Preview update for Windows 11 version 24H2, was released on April 11, 2025, in the Beta Channel for Windows Insiders, updating
 Please Wait While BIOS Backup Processing, Pro Guide to RemoveApr 13, 2025 pm 08:03 PM
Please Wait While BIOS Backup Processing, Pro Guide to RemoveApr 13, 2025 pm 08:03 PMEncountering the persistent "Please wait while BIOS backup processing" message during startup? This guide offers solutions to resolve this annoying Lenovo issue, often appearing after Windows installation or updates. Before proceeding, it'
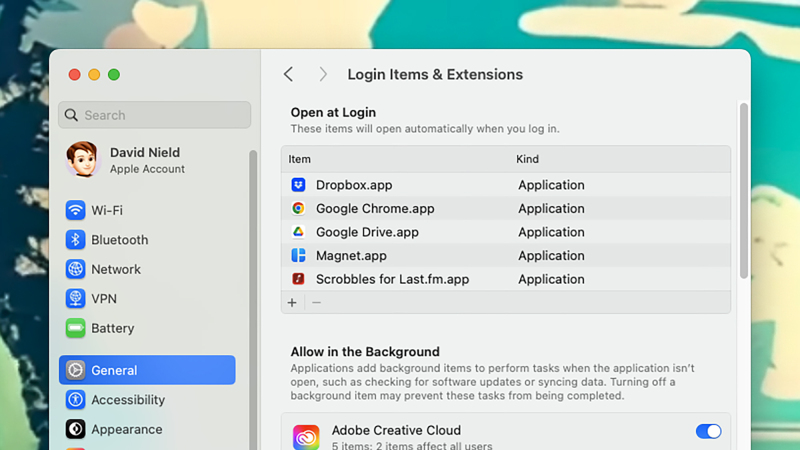 How to keep your old computer running for as long as possibleApr 13, 2025 am 10:17 AM
How to keep your old computer running for as long as possibleApr 13, 2025 am 10:17 AMYou want to squeeze as much life from a laptop or desktop computer as possible. Doing so can save a substantial amount of money over time, and stops you from contributing to mountains of e-waste. At the same time, dealing with an old, sluggish


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Safe Exam Browser
Safe Exam Browser is a secure browser environment for taking online exams securely. This software turns any computer into a secure workstation. It controls access to any utility and prevents students from using unauthorized resources.

MantisBT
Mantis is an easy-to-deploy web-based defect tracking tool designed to aid in product defect tracking. It requires PHP, MySQL and a web server. Check out our demo and hosting services.

SecLists
SecLists is the ultimate security tester's companion. It is a collection of various types of lists that are frequently used during security assessments, all in one place. SecLists helps make security testing more efficient and productive by conveniently providing all the lists a security tester might need. List types include usernames, passwords, URLs, fuzzing payloads, sensitive data patterns, web shells, and more. The tester can simply pull this repository onto a new test machine and he will have access to every type of list he needs.

ZendStudio 13.5.1 Mac
Powerful PHP integrated development environment











