Ransomware is a powerful cyber threat because the procedure of file-locking is there for money demands and direct extortion purposes.[1] These cybercriminals encrypt files and change the original code of the document or image, video, or audio file, so the marker .dfwe appears at the end of every filename after the file type indicator.
These infection symptoms are only noticed when data is locked, marked, and the ransomware note _readme.txt is delivered to the screen. This text file gets laced in various folders with encoded data and it informs victims about what happened. However, the message includes false claims.
Dfwe ransomware creators try to encourage or even scare people into paying the ransom demand. Those promises, discount offers, and other claims are there to fake legitimacy and trust. Paying the ransom even tough with a discount is not going to guarantee the file recovery. Rely on removal procedures and alternate methods.

1. Decrypt the locked data
Decryption is the only process that could recover files fully and without additional damage caused to the machine or other files. The tool for this Dfwe file virus version does not exist. The threat actors claim to have the needed tool and offer to release this opportunity for you after the payment, however, that is not guaranteed and criminals should not be trusted.
The family of Djvu virus that this threat comes from is using advanced methods for file locking, so variants are not decryptable. The option was previously available because of the decryption keys used by the versions at the beginning. The offline keys that were used before provided the decryption for all of the victims with one obtained key.
If the offline key is used during encryption all devices affected by the same variant receive the same key. As for the online IDs the virus forms those with each encryption procedure and makes the unique key for each affected device. This is the method primarily used by the Dfwe ransomware virus too. These processes often can still fail, so try to check for the decryption option.
- Download the app on official Emsisoft website.
- Once decrypt_STOPDjvu.exe shows up – click it.
- Follow the steps on the screen.
- The tool should locate the affected folders.

- You can also do it by pressing Add folder at the bottom.
- Press Decrypt.

- There are particular results that can occur indicating if the decryption is possible.
2. Eliminate the ransomware virus
Malware can be intrusive and silent at the same time. The distribution of the cryptovirus is including the malicious files delivered behind users' backs. The removal of the Dfwe ransomware becomes more difficult due to these distribution methods[2] and the fact that other threats get installed during the infiltration too.
These threats focused on cryptocurrency extortion can be distributed and hit those common files with the encryption procedure later on. You need to remove the threat as soon as possible once these files get locked and marked, so you can properly avoid damaging processes following the encryption.
Dfwe ransomware virus removal process can be quick and effortless if you base the procedure on the anti-malware tools and virus detection[3] rates. These antivirus programs can find all malicious programs and infections, so the active virus is stopped and no longer running on the machine.
3. Restore corrupted system data
- Install FortectMac Washing Machine X9.
- Run the full system scan and wait for the complete analysis.
- Follow the on-screen steps.
- Allow the machine to get checked.
- Check the Summary.

- You can fix issues manually from the list.
- Purchasing a licensed version can help repair serious issues.
4. Recover damaged files
- Get a tool like Data Recovery Pro from a trustworthy source.
- Follow installation instructions.
- Once that is finished, use the application.
- Select Everything or pick individual folders to recover.
- Press Next.

- Enable Deep scan at the bottom.
- Pick which Disk you want to be scanned.
- Scan.

- Hit Recover to restore files.
The above is the detailed content of How to recover .dfwe locked files?. For more information, please follow other related articles on the PHP Chinese website!
 Clipchamp Video Loss on Windows? 2 Ways to Recover Files!May 09, 2025 pm 08:12 PM
Clipchamp Video Loss on Windows? 2 Ways to Recover Files!May 09, 2025 pm 08:12 PMRecover Lost Clipchamp Videos: A Step-by-Step Guide Losing a video you've edited in Clipchamp can be frustrating. This guide provides effective methods to recover your lost Clipchamp video files. Finding Your Clipchamp Videos Before attempting recov
 7 Useful Fixes for Action Center Keeps Popping upMay 09, 2025 pm 08:07 PM
7 Useful Fixes for Action Center Keeps Popping upMay 09, 2025 pm 08:07 PMAction Center allows you to access quick settings and notifications. However, some users say that they encounter the “Action Center keeps popping up” issue on Windows 11/10. If you are one of them, refer to this post from MiniTool to get solutions.Qu
 Instant Ways to Restore Missing Google Chrome Icon on WindowsMay 09, 2025 pm 08:06 PM
Instant Ways to Restore Missing Google Chrome Icon on WindowsMay 09, 2025 pm 08:06 PMTroubleshoot Missing Google Chrome Icon on Windows Can't find your Google Chrome icon on Windows? This guide offers several solutions to restore it. Why is my Chrome icon missing? Several factors can cause the Chrome icon to vanish from your desktop:
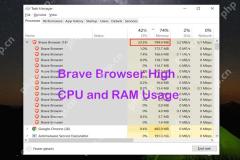 Brave Browser High CPU and RAM Usage: Best 5 Tips to ReduceMay 09, 2025 pm 08:05 PM
Brave Browser High CPU and RAM Usage: Best 5 Tips to ReduceMay 09, 2025 pm 08:05 PMBrave browser CPU and memory usage too high? Under Windows 10/11 system, Brave browser's high CPU and memory usage problems have troubled many users. This tutorial will provide a variety of solutions to help you easily resolve this issue. Quick navigation: Brave browser high CPU and memory footprint Solution 1: Clear cookies and cache data Solution 2: Disable hardware acceleration Solution 3: Close the tab and update the Brave browser Solution 4: Disable the plugin Solution 5: Create a new user profile Optional: Run MiniTool System Booster System Optimization Tool Summarize Brave browser high CP
 Targeted Fixes for Xbox Error 0x87e0000f When Installing GamesMay 09, 2025 pm 08:04 PM
Targeted Fixes for Xbox Error 0x87e0000f When Installing GamesMay 09, 2025 pm 08:04 PMTroubleshooting Xbox Error Code 0x87e0000f: A Comprehensive Guide Encountering the Xbox error code 0x87e0000f while downloading games from Xbox Game Pass can be frustrating. This guide provides several solutions to help you resolve this issue and get
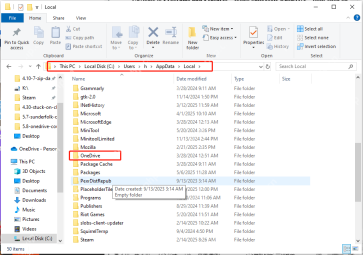 OneDrive Couldn't Start Files on Demand?Top 4 MethodsMay 09, 2025 pm 08:02 PM
OneDrive Couldn't Start Files on Demand?Top 4 MethodsMay 09, 2025 pm 08:02 PMOneDrive Files On-Demand troubleshooting: resolving the "OneDrive couldn't start Files On-Demand" error. This MiniTool guide provides solutions for the persistent "Microsoft OneDrive Couldn’t start files on Demand" error (codes 0x
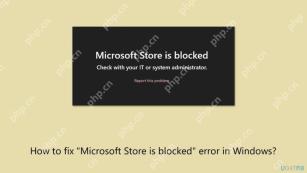 How to fix 'Microsoft Store is blocked' error in Windows?May 09, 2025 pm 06:00 PM
How to fix 'Microsoft Store is blocked' error in Windows?May 09, 2025 pm 06:00 PMMicrosoft Store is blocked error occurs when Windows prevents access to the Microsoft Store app, displaying the message Microsoft Store is blocked. Check with y
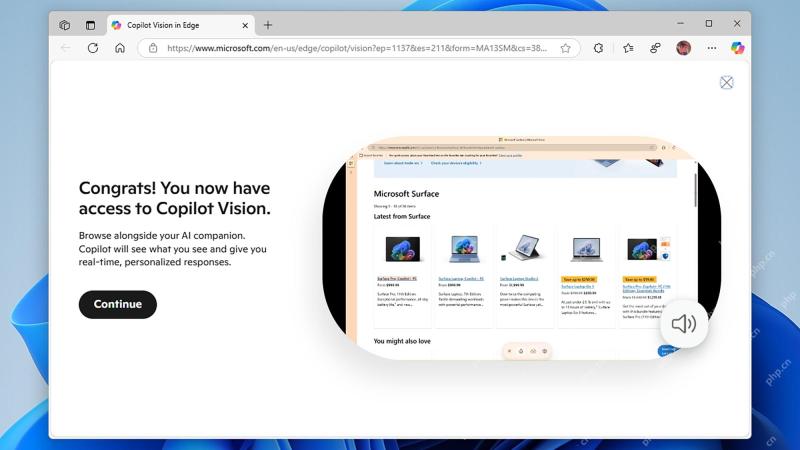 How to use Copilot Vision for free in Microsoft EdgeMay 09, 2025 am 10:32 AM
How to use Copilot Vision for free in Microsoft EdgeMay 09, 2025 am 10:32 AMStaying current with all the new AI tools is a challenge. Many might even overlook readily available AI features. For instance, Copilot Vision is now free for all Microsoft Edge users – a fact easily missed if you don't regularly use Edge or haven't


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

SublimeText3 English version
Recommended: Win version, supports code prompts!

SAP NetWeaver Server Adapter for Eclipse
Integrate Eclipse with SAP NetWeaver application server.

WebStorm Mac version
Useful JavaScript development tools

MinGW - Minimalist GNU for Windows
This project is in the process of being migrated to osdn.net/projects/mingw, you can continue to follow us there. MinGW: A native Windows port of the GNU Compiler Collection (GCC), freely distributable import libraries and header files for building native Windows applications; includes extensions to the MSVC runtime to support C99 functionality. All MinGW software can run on 64-bit Windows platforms.

SublimeText3 Linux new version
SublimeText3 Linux latest version












