The infection that focuses on the file locking functions and money demands from the victim can spread silently and cause the issues with the targeted machine without triggering any seen symptoms for the victim. users may notice speed or performance issues when the encryption[1] algorithm is running and changing the original code of the found files.
Nnuz ransomware can affect images, audio, video files, and particular documents that look valuable or are commonly used, so can be indicated as important to the victim. These files are chosen, so the victim can be more eager to pay up when the affected data is important.
The extension that appears at the end of the original filename is indicating the name of this particular file-locker virus. This unique marker .nnuz is added to the end of the file, so the Picture.jpg becomes Picture.jpg.nnuz, and the original code is altered, so the file cannot be opened.
This is the main reason for the ransom demands[2] and the purpose of the encryption. These threats are focused on altering data and demanding money. The direct payment of $980 in Bitcoin is asked via the ransom message that gets listed in the _readme.txt file. You should ignore these claims and scare tactics and move on with Nnuz file virus removal.

1. Remove the active threat
Virus creators often rely on other programs and deceptive, promotional sites that can spread the infection around the world. This ransomware can distribute the payload with eh help of other malware like trojans, worms, and macro viruses. these are methods more often used to deliver the initial virus.
Once the spam email attachment is opened or the malicious program downloaded on the machine, Nnuz ransomware can start the encryption process once the infiltration is completed. This is the main process, but other viruses and different files get added to the machine to keep the infection persistent.
You can and should remove the infection by running an anti-malware tool or security program, so the system is checked fully and all potential threats removed. You must rely on proper AV tools and security programs that are relying on AV detection[3] and can terminate any intruders found on the system.
2. Decrypt the locked files
The threat is related to Djvu virus family that released the latest versions Dfwe and Fdcv recently. This family has versions coming out each week and sometimes three or four at a time. Samples of this family flood the internet and users cannot find the solution for the encryption because this is the malware that has updated the techniques.
These issues with advanced malware and encryption methods mean that the Nnuz file virus is not decryptable because these methods used during encryption rely on online keys and these are unique per every affected device. The infection can connect to the remote server and make the different keys for the decryption procedure.
Offline IDs, if used, can be specific to the version of the ransomware only, so helps with decryption for many victims at the time. It is rare, but these threats might fail to communicate with the servers and offline keys get used. If so, you can check the options for decryption.
- Download the app on official Emsisoft website.
- Once decrypt_STOPDjvu.exe shows up – click it.
- Follow the steps on the screen.
- The tool should locate the affected folders.
- You can also do it by pressing Add folder at the bottom.

- Press Decrypt.

- There are particular results that can occur indicating if the decryption is possible.
From here, there are three available outcomes:
- “Decrypted!” will be shown under files that were decrypted successfully – they are now usable again.
- “Error: Unable to decrypt file with ID:” means that the keys for this version of the virus have not yet been retrieved, so you should try later.
- “This ID appears to be an online ID, decryption is impossible” – you are unable to decrypt files with this tool.
3. Restore corrupted system data
- Install FortectMac Washing Machine X9.
- Run the full system scan and wait for the complete analysis.
- Follow the on-screen steps.
- Allow the machine to get checked.
- Check the Summary.

- You can fix issues manually from the list.
- Purchasing a licensed version can help repair serious issues.
4. Recover the data with an app
- Get a tool like Data Recovery Pro from a trustworthy source.
- Follow installation instructions.
- Once that is finished, use the application.
- Select Everything or pick individual folders to recover.
- Press Next.

- Enable Deep scan at the bottom.
- Pick which Disk you want to be scanned.
- Scan.

- Hit Recover to restore files.
The above is the detailed content of How to recover .nnuz files?. For more information, please follow other related articles on the PHP Chinese website!
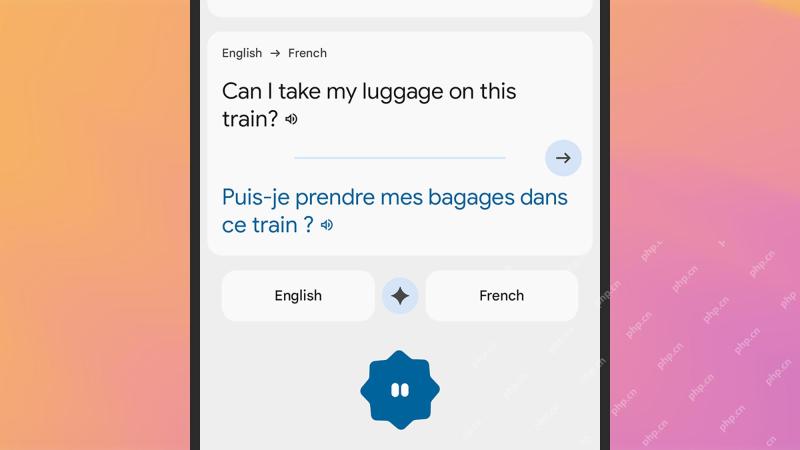 How to get real-time translations on your phoneMay 06, 2025 am 09:44 AM
How to get real-time translations on your phoneMay 06, 2025 am 09:44 AMAI-powered mobile translation apps have dramatically improved real-time conversation capabilities. With a strong internet connection, most apps now seamlessly translate spoken words, eliminating the need for manual typing or pronunciation struggles.
 How to fix Windows update error 0x80071160?May 05, 2025 pm 10:00 PM
How to fix Windows update error 0x80071160?May 05, 2025 pm 10:00 PMWhile many users dont realize that, Windows updates are among the most important features for maintaining the systems stability and security, as well as ensurin
 Must-Know Things: What to Check When Buying a Used LaptopMay 05, 2025 pm 08:01 PM
Must-Know Things: What to Check When Buying a Used LaptopMay 05, 2025 pm 08:01 PMThis MiniTool guide provides essential checks before buying a used laptop. It details how to assess the physical condition, test key hardware, and evaluate the software to ensure a sound purchase. Quick Navigation: What to Check When Buying a Used
 What to Do Before Replacing a Hard Drive? Learn Essentials!May 04, 2025 pm 08:02 PM
What to Do Before Replacing a Hard Drive? Learn Essentials!May 04, 2025 pm 08:02 PMUpgrade the hard drive and improve the computer performance! This article will guide you the steps you need to take before replacing a hard drive on your Windows computer with a larger disk or SSD to avoid unnecessary hassle. Preparation: Choose the right hard drive: When choosing a hard disk, you should not only consider the difference between SSD and HDD, but also consider factors such as storage capacity, form factor size and budget. SSD capacity ranges from 256GB to 4TB or even larger, choose the capacity that suits your needs. Also, check which SSD slot is used for your laptop or desktop and make sure that the SSD you choose (such as 2.5-inch and 3.5-inch SATA SSD, M.2 2280/2230/2242 SSD, etc.) is compatible with your computer. Finally, according to
 Sultan's Game Save File Location: A Detailed Roadmap GuideMay 04, 2025 pm 08:01 PM
Sultan's Game Save File Location: A Detailed Roadmap GuideMay 04, 2025 pm 08:01 PMMastering Sultan's Game: Save File Location and Backup Strategies This guide helps you locate and protect your Sultan's Game save files. Released on March 31st, 2025, Sultan's Game's engaging narratives and appealing visuals have made it a popular c
 A Step-by-Step Guide to Copy ESXi VM to a USB DriveMay 03, 2025 pm 08:01 PM
A Step-by-Step Guide to Copy ESXi VM to a USB DriveMay 03, 2025 pm 08:01 PMOffsite VM backups are crucial. This guide demonstrates how to easily copy ESXi virtual machines to a USB drive for secure, accessible storage. Method 1: Manual VM File Download This method copies the core VM files. Power off the target VM in the V
 Windows 10 KB5055612: New Features & What if It Failed to InstallMay 02, 2025 pm 08:01 PM
Windows 10 KB5055612: New Features & What if It Failed to InstallMay 02, 2025 pm 08:01 PMThis non-security update, KB5055612 for Windows 10 version 22H2 and related versions, released April 22, 2025, offers several quality improvements. This guide details installation and troubleshooting steps. KB5055612: Key Improvements This update enh
 Unlock Helpful Methods to Fix KB5055642 Not InstallingMay 02, 2025 pm 06:01 PM
Unlock Helpful Methods to Fix KB5055642 Not InstallingMay 02, 2025 pm 06:01 PMTroubleshooting KB5055642 Installation Problems on Windows 11 This guide offers solutions for users encountering issues installing Windows 11 Insider Preview Build 26200.5562 (KB5055642), released April 21, 2025. This update introduces enhanced featu


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

SublimeText3 Linux new version
SublimeText3 Linux latest version

Dreamweaver Mac version
Visual web development tools

WebStorm Mac version
Useful JavaScript development tools

PhpStorm Mac version
The latest (2018.2.1) professional PHP integrated development tool

DVWA
Damn Vulnerable Web App (DVWA) is a PHP/MySQL web application that is very vulnerable. Its main goals are to be an aid for security professionals to test their skills and tools in a legal environment, to help web developers better understand the process of securing web applications, and to help teachers/students teach/learn in a classroom environment Web application security. The goal of DVWA is to practice some of the most common web vulnerabilities through a simple and straightforward interface, with varying degrees of difficulty. Please note that this software












