Unleash the Power of Deepseek: Discover Hidden Treasures Online
This article explores the capabilities of Deepseek, a hypothetical advanced search engine designed to uncover information hidden from standard search engines. We will address its unique functionalities and user-friendliness.
Deepseek's Unique Approach to Information Retrieval
Deepseek's power lies in its multi-faceted approach to online searching. Unlike traditional search engines that primarily rely on keyword matching and indexed web pages, Deepseek utilizes several advanced techniques. These include:
- Deep Web Crawling: Deepseek actively crawls the deep web, a vast portion of the internet inaccessible to standard search engines. This includes content behind logins, dynamic web pages generated on demand, and databases not indexed by conventional methods. This access significantly expands the scope of searchable information.
- Semantic Search: Instead of simply matching keywords, Deepseek employs semantic search algorithms. This means it understands the meaning and context of your search query, enabling it to retrieve relevant information even if the exact keywords aren't present. This allows for more nuanced and accurate results.
- Data Mining and Analysis: Deepseek incorporates data mining techniques to analyze the relationships between different pieces of information. This helps uncover hidden connections and patterns that would otherwise be missed. This is particularly useful for identifying obscure or fragmented data sources.
- Advanced Filtering and Customization: Deepseek offers sophisticated filtering options allowing users to refine their searches based on various criteria such as file type, date range, language, and source credibility. This helps users narrow down their search results and focus on relevant information.
How can Deepseek help me find information not easily accessible through standard search engines?
Deepseek excels at finding information hidden from standard search engines due to its access to the deep web and its advanced search algorithms. For example, it can help locate:
- Archived or Obscure Web Pages: Deepseek can access archived versions of websites and uncover pages that have been removed or are no longer easily indexed.
- Data Behind Logins: If you have access credentials, Deepseek can retrieve information from member-only websites, forums, and databases.
- Information in Unindexed Databases: Deepseek can search through databases that are not indexed by standard search engines, allowing access to specialized information not readily available to the public.
- Specific File Types: Deepseek allows users to specify the desired file type (e.g., PDF, DOCX, XLSX) to find specific documents related to their query.
- Hidden Links and Resources: Deepseek can uncover links and resources buried deep within websites, forums, or online communities, leading users to information that is not readily apparent.
What types of hidden online treasures can I expect to uncover using Deepseek?
The types of information you can uncover with Deepseek are as diverse as the internet itself. Examples include:
- Rare historical documents: Deepseek can help researchers find archived documents, academic papers, or government records not readily available online.
- Specialized research data: Researchers can access niche datasets and databases relevant to their specific fields of study.
- Hidden online communities and forums: Deepseek can uncover communities and forums discussing specific topics, providing access to insider knowledge and perspectives.
- Unique multimedia content: Deepseek can locate rare videos, images, or audio files that are not indexed by standard search engines.
- Market research data: Businesses can use Deepseek to access market research data and competitor information.
Is Deepseek suitable for both beginners and experienced online researchers?
Yes, Deepseek is designed to be user-friendly for both beginners and experienced online researchers. Its intuitive interface and comprehensive help resources make it accessible to those with limited search experience. However, its advanced features and capabilities offer significant advantages to experienced researchers who can leverage its power to conduct in-depth investigations and uncover truly hidden information. The customizable filtering options allow users of all levels to tailor their searches to their specific needs and expertise.
The above is the detailed content of Unleash the Power of Deepseek: Discover Hidden Treasures Online. For more information, please follow other related articles on the PHP Chinese website!
 A Business Leader's Guide To Generative Engine Optimization (GEO)May 03, 2025 am 11:14 AM
A Business Leader's Guide To Generative Engine Optimization (GEO)May 03, 2025 am 11:14 AMGoogle is leading this shift. Its "AI Overviews" feature already serves more than one billion users, providing complete answers before anyone clicks a link.[^2] Other players are also gaining ground fast. ChatGPT, Microsoft Copilot, and Pe
 This Startup Is Using AI Agents To Fight Malicious Ads And Impersonator AccountsMay 03, 2025 am 11:13 AM
This Startup Is Using AI Agents To Fight Malicious Ads And Impersonator AccountsMay 03, 2025 am 11:13 AMIn 2022, he founded social engineering defense startup Doppel to do just that. And as cybercriminals harness ever more advanced AI models to turbocharge their attacks, Doppel’s AI systems have helped businesses combat them at scale— more quickly and
 How World Models Are Radically Reshaping The Future Of Generative AI And LLMsMay 03, 2025 am 11:12 AM
How World Models Are Radically Reshaping The Future Of Generative AI And LLMsMay 03, 2025 am 11:12 AMVoila, via interacting with suitable world models, generative AI and LLMs can be substantively boosted. Let’s talk about it. This analysis of an innovative AI breakthrough is part of my ongoing Forbes column coverage on the latest in AI, including
 May Day 2050: What Have We Left To Celebrate?May 03, 2025 am 11:11 AM
May Day 2050: What Have We Left To Celebrate?May 03, 2025 am 11:11 AMLabor Day 2050. Parks across the nation fill with families enjoying traditional barbecues while nostalgic parades wind through city streets. Yet the celebration now carries a museum-like quality — historical reenactment rather than commemoration of c
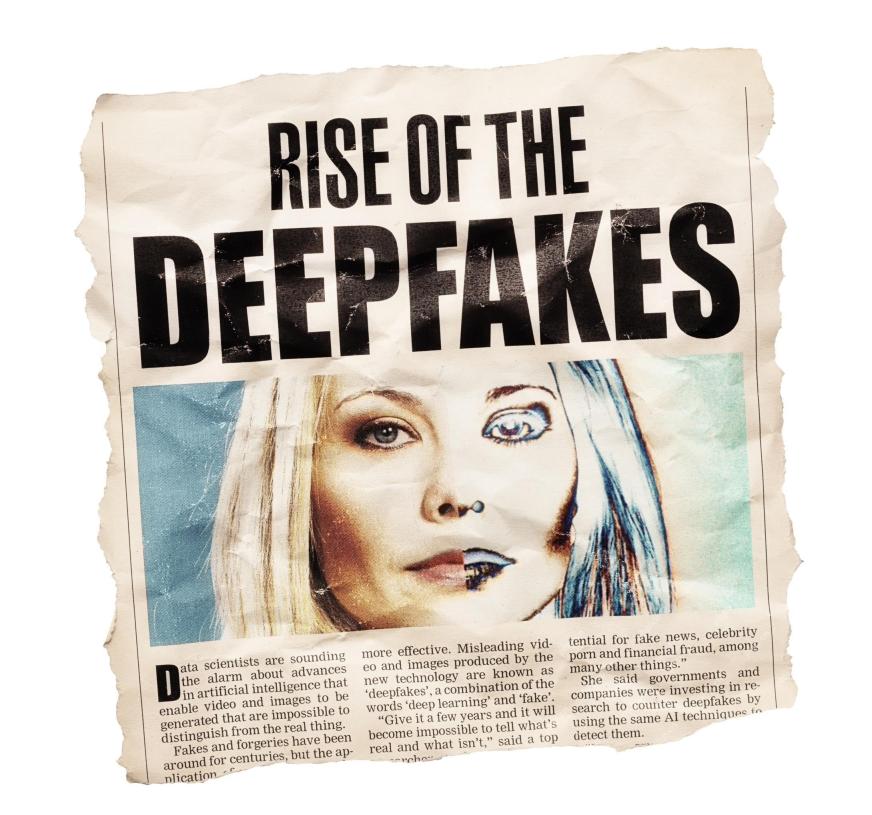 The Deepfake Detector You've Never Heard Of That's 98% AccurateMay 03, 2025 am 11:10 AM
The Deepfake Detector You've Never Heard Of That's 98% AccurateMay 03, 2025 am 11:10 AMTo help address this urgent and unsettling trend, a peer-reviewed article in the February 2025 edition of TEM Journal provides one of the clearest, data-driven assessments as to where that technological deepfake face off currently stands. Researcher
 Quantum Talent Wars: The Hidden Crisis Threatening Tech's Next FrontierMay 03, 2025 am 11:09 AM
Quantum Talent Wars: The Hidden Crisis Threatening Tech's Next FrontierMay 03, 2025 am 11:09 AMFrom vastly decreasing the time it takes to formulate new drugs to creating greener energy, there will be huge opportunities for businesses to break new ground. There’s a big problem, though: there’s a severe shortage of people with the skills busi
 The Prototype: These Bacteria Can Generate ElectricityMay 03, 2025 am 11:08 AM
The Prototype: These Bacteria Can Generate ElectricityMay 03, 2025 am 11:08 AMYears ago, scientists found that certain kinds of bacteria appear to breathe by generating electricity, rather than taking in oxygen, but how they did so was a mystery. A new study published in the journal Cell identifies how this happens: the microb
 AI And Cybersecurity: The New Administration's 100-Day ReckoningMay 03, 2025 am 11:07 AM
AI And Cybersecurity: The New Administration's 100-Day ReckoningMay 03, 2025 am 11:07 AMAt the RSAC 2025 conference this week, Snyk hosted a timely panel titled “The First 100 Days: How AI, Policy & Cybersecurity Collide,” featuring an all-star lineup: Jen Easterly, former CISA Director; Nicole Perlroth, former journalist and partne


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

mPDF
mPDF is a PHP library that can generate PDF files from UTF-8 encoded HTML. The original author, Ian Back, wrote mPDF to output PDF files "on the fly" from his website and handle different languages. It is slower than original scripts like HTML2FPDF and produces larger files when using Unicode fonts, but supports CSS styles etc. and has a lot of enhancements. Supports almost all languages, including RTL (Arabic and Hebrew) and CJK (Chinese, Japanese and Korean). Supports nested block-level elements (such as P, DIV),

DVWA
Damn Vulnerable Web App (DVWA) is a PHP/MySQL web application that is very vulnerable. Its main goals are to be an aid for security professionals to test their skills and tools in a legal environment, to help web developers better understand the process of securing web applications, and to help teachers/students teach/learn in a classroom environment Web application security. The goal of DVWA is to practice some of the most common web vulnerabilities through a simple and straightforward interface, with varying degrees of difficulty. Please note that this software

Dreamweaver Mac version
Visual web development tools

SecLists
SecLists is the ultimate security tester's companion. It is a collection of various types of lists that are frequently used during security assessments, all in one place. SecLists helps make security testing more efficient and productive by conveniently providing all the lists a security tester might need. List types include usernames, passwords, URLs, fuzzing payloads, sensitive data patterns, web shells, and more. The tester can simply pull this repository onto a new test machine and he will have access to every type of list he needs.

SublimeText3 Mac version
God-level code editing software (SublimeText3)







