Deleting files from your computer doesn't mean they vanish instantly. Even emptying the Recycle Bin or Trash merely flags the space as available; the data persists until overwritten. This explains why data recovery tools exist. However, for sensitive data or when selling a device, permanent deletion is crucial. This guide ensures unwanted files are irretrievable, even by expert forensic teams. Remember, this is irreversible.
First, delete the file via File Explorer (Windows) or Finder (macOS), then empty the Recycle Bin/Trash. This is insufficient for secure deletion.
Permanent Deletion from Standard Hard Drives (HDDs)

Older computers use HDDs, where data is stored contiguously, making recovery easier. Third-party tools are necessary for secure deletion. Eraser (Windows) or Recuva (Windows, also a recovery tool) overwrite the space with random data. For Macs with HDDs, Permanent Eraser (newer Macs) is recommended. Older Macs running Yosemite or earlier can use the "Secure Empty Trash" function (Finder menu). Note: Apple removed this from El Capitan onwards due to the prevalence of SSDs.
Permanent Deletion from Solid-State Drives (SSDs)

SSDs, faster but more expensive, handle deletions differently. Overwrite tools are ineffective. Encryption is the solution. Your login credentials act as the unlock key; without them, deleted files are inaccessible. The risk is compromised credentials. Use strong passwords.
Macs generally auto-encrypt; verify via System Settings > Privacy & Security > FileVault (or System Preferences > Security & Privacy > FileVault on pre-Ventura). Windows 10/11 Pro/Enterprise/Education versions use BitLocker; otherwise, VeraCrypt is a free alternative.
For complete device erasure before selling, transfer data, back it up, and reinstall the operating system. Follow Apple's instructions for macOS or use Windows reset or SSD manufacturer tools (SanDisk, OCZ, Samsung, etc.) for a full wipe.
Permanent Deletion on Tablets and Phones

Tablets and phones use flash storage (like SSDs). Secure deletion is impractical; encryption is key. Limited app access to file systems makes recovery extremely difficult. Prioritize strong lock screen security (fingerprint ID or PIN). iOS and Android (6.0 ) encrypt by default.
For device disposal, factory reset is recommended (iOS: Settings > General > Transfer or Reset Phone > Reset; Android: Settings > System > Reset options > Erase all data (factory reset)). While technically recoverable, it requires extraordinary expertise.
Finally, for ultimate paranoia, physical destruction (hammering the drive/phone) guarantees data irretrievability.
This article has been updated.
The above is the detailed content of Permanently delete files (for real). For more information, please follow other related articles on the PHP Chinese website!
 How to fix Microsoft Teams Error tag 7ita9 in Windows?May 06, 2025 pm 04:00 PM
How to fix Microsoft Teams Error tag 7ita9 in Windows?May 06, 2025 pm 04:00 PMMicrosoft Teams is widely used for virtual meetings, team collaboration, and workplace communication. But from time to time, users encounter technical issues th
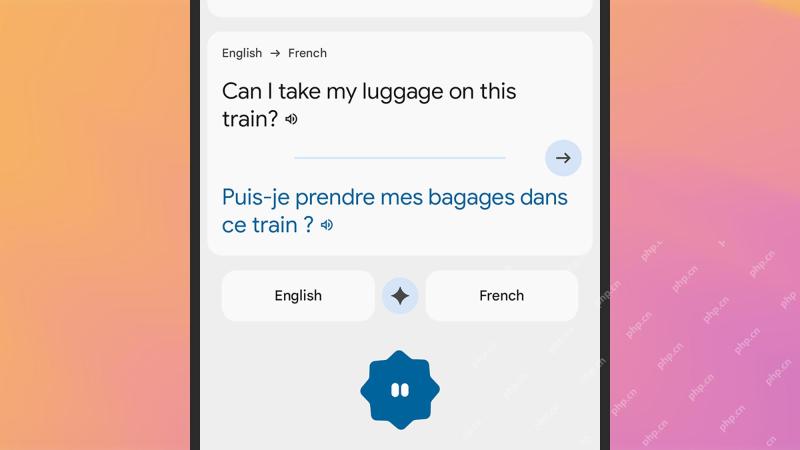 How to get real-time translations on your phoneMay 06, 2025 am 09:44 AM
How to get real-time translations on your phoneMay 06, 2025 am 09:44 AMAI-powered mobile translation apps have dramatically improved real-time conversation capabilities. With a strong internet connection, most apps now seamlessly translate spoken words, eliminating the need for manual typing or pronunciation struggles.
 How to fix Windows update error 0x80071160?May 05, 2025 pm 10:00 PM
How to fix Windows update error 0x80071160?May 05, 2025 pm 10:00 PMWhile many users dont realize that, Windows updates are among the most important features for maintaining the systems stability and security, as well as ensurin
 Must-Know Things: What to Check When Buying a Used LaptopMay 05, 2025 pm 08:01 PM
Must-Know Things: What to Check When Buying a Used LaptopMay 05, 2025 pm 08:01 PMThis MiniTool guide provides essential checks before buying a used laptop. It details how to assess the physical condition, test key hardware, and evaluate the software to ensure a sound purchase. Quick Navigation: What to Check When Buying a Used
 What to Do Before Replacing a Hard Drive? Learn Essentials!May 04, 2025 pm 08:02 PM
What to Do Before Replacing a Hard Drive? Learn Essentials!May 04, 2025 pm 08:02 PMUpgrade the hard drive and improve the computer performance! This article will guide you the steps you need to take before replacing a hard drive on your Windows computer with a larger disk or SSD to avoid unnecessary hassle. Preparation: Choose the right hard drive: When choosing a hard disk, you should not only consider the difference between SSD and HDD, but also consider factors such as storage capacity, form factor size and budget. SSD capacity ranges from 256GB to 4TB or even larger, choose the capacity that suits your needs. Also, check which SSD slot is used for your laptop or desktop and make sure that the SSD you choose (such as 2.5-inch and 3.5-inch SATA SSD, M.2 2280/2230/2242 SSD, etc.) is compatible with your computer. Finally, according to
 Sultan's Game Save File Location: A Detailed Roadmap GuideMay 04, 2025 pm 08:01 PM
Sultan's Game Save File Location: A Detailed Roadmap GuideMay 04, 2025 pm 08:01 PMMastering Sultan's Game: Save File Location and Backup Strategies This guide helps you locate and protect your Sultan's Game save files. Released on March 31st, 2025, Sultan's Game's engaging narratives and appealing visuals have made it a popular c
 A Step-by-Step Guide to Copy ESXi VM to a USB DriveMay 03, 2025 pm 08:01 PM
A Step-by-Step Guide to Copy ESXi VM to a USB DriveMay 03, 2025 pm 08:01 PMOffsite VM backups are crucial. This guide demonstrates how to easily copy ESXi virtual machines to a USB drive for secure, accessible storage. Method 1: Manual VM File Download This method copies the core VM files. Power off the target VM in the V
 Windows 10 KB5055612: New Features & What if It Failed to InstallMay 02, 2025 pm 08:01 PM
Windows 10 KB5055612: New Features & What if It Failed to InstallMay 02, 2025 pm 08:01 PMThis non-security update, KB5055612 for Windows 10 version 22H2 and related versions, released April 22, 2025, offers several quality improvements. This guide details installation and troubleshooting steps. KB5055612: Key Improvements This update enh


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Dreamweaver Mac version
Visual web development tools

VSCode Windows 64-bit Download
A free and powerful IDE editor launched by Microsoft

SublimeText3 Chinese version
Chinese version, very easy to use

MinGW - Minimalist GNU for Windows
This project is in the process of being migrated to osdn.net/projects/mingw, you can continue to follow us there. MinGW: A native Windows port of the GNU Compiler Collection (GCC), freely distributable import libraries and header files for building native Windows applications; includes extensions to the MSVC runtime to support C99 functionality. All MinGW software can run on 64-bit Windows platforms.

SecLists
SecLists is the ultimate security tester's companion. It is a collection of various types of lists that are frequently used during security assessments, all in one place. SecLists helps make security testing more efficient and productive by conveniently providing all the lists a security tester might need. List types include usernames, passwords, URLs, fuzzing payloads, sensitive data patterns, web shells, and more. The tester can simply pull this repository onto a new test machine and he will have access to every type of list he needs.






