 Web Front-end
Web Front-end JS Tutorial
JS Tutorial How to Kill Vulnerabilities in Your Node.js App: A Guide to Writing Secure JavaScript Code
How to Kill Vulnerabilities in Your Node.js App: A Guide to Writing Secure JavaScript Code
Js/Ts and Node.js have revolutionized the software engineering world, but with great power comes great responsibility?️. With so many packages and the fast pace of engineering, vulnerabilities are bound to sneak in. In this article, we’ll tackle the most common vulnerabilities lurking in the JavaScript ecosystem and show you exactly how to “kill” them with secure code practices.
1. Dependency Vulnerabilities
Problem: The JavaScript ecosystem relies heavily on packages from places like npm. When you install these packages, you often pull in additional dependencies. Unfortunately, not all packages are maintained with security in mind, and some even come with malicious code intentionally.
Solution:
- Audit Dependencies: Run npm audit to check for any known vulnerabilities in your dependencies. This will give you a report and suggestions for fixing issues.
- Regularly Update Packages: Use npm outdated to check for outdated packages, especially those with security patches. Staying up-to-date helps prevent vulnerabilities.
- Use Security-Focused Tools: Tools like Snyk or OWASP Dependency-Check scan your dependencies for known vulnerabilities.
2. Insecure Configurations
Problem: Leaving default configurations, especially in production, can expose your application to attackers. Things like enabling verbose logging, leaving debug modes on, or allowing CORS for all origins can create security holes.
Solution:
- Environment-Specific Configurations: Set different configurations for development and production. For example, disable debug mode and reduce logging in production.
- Environment Variables: Keep sensitive information (e.g., database credentials, API keys) in environment variables and use libraries like dotenv to manage them securely.
- Use a .env File for Sensitive Data: Never store credentials or sensitive data in your codebase. Use a .env file, and don’t forget to add it to .gitignore.
3. Injection Attacks (SQL/NoSQL Injection)
Problem: Injection attacks happen when user input is incorrectly processed and treated as executable code or a database command. For instance, SQL injection can allow attackers to manipulate database queries and access sensitive data.
Solution:
- Parameterized Queries: Always use parameterized or prepared statements when interacting with databases. Libraries like pg for PostgreSQL or mongoose for MongoDB support these secure methods.
- Sanitize User Input: Use a library like validator to sanitize input, especially when dealing with forms or other sources of user input.
4. Cross-Site Scripting (XSS)
Problem: XSS attacks happen when attackers inject malicious scripts into your application. For example, if your app displays user-generated content without sanitizing it, an attacker could inject JavaScript that gets executed by other users’ browsers.
Solution:
- Escape User Input: Make sure that any user-generated content displayed on the front end is escaped. This way, it’s treated as plain text and not as executable code.
- Content Security Policy (CSP): A CSP allows you to define which scripts, images, and styles are allowed to run on your website. It’s a powerful way to limit XSS attacks. You can set up a CSP header in your server configuration.
- Use a Trusted Library: If you use templating libraries (e.g., Handlebars, EJS), they often have built-in escaping features. Don’t disable them.
5. Cross-Site Request Forgery (CSRF)
Problem: CSRF attacks trick users into executing unwanted actions on a different website where they’re authenticated. For example, a user logged into their bank account could unknowingly transfer money to another account by clicking a link in a malicious email.
Solution:
- Use CSRF Tokens: When using forms, implement CSRF tokens to verify that each request is legitimate. Many frameworks, such as Express, have middleware like csurf to help prevent CSRF attacks.
- Double Submit Cookies: This is another approach where you set a unique token in a cookie and require the same token to be submitted in the request payload.
const express = require('express');
const csurf = require('csurf');
const cookieParser = require('cookie-parser');
const app = express();
// Use cookie parser and csrf middleware
app.use(cookieParser());
app.use(csurf({ cookie: true }));
// Middleware to add CSRF token to all responses
app.use((req, res, next) => {
res.locals.csrfToken = req.csrfToken();
next();
});
app.get('/form', (req, res) => {
// Render a form with the CSRF token
res.send(`
`);
});
app.post('/submit', (req, res) => {
res.send('Data received securely!');
});
app.listen(3000, () => console.log('Server running on http://localhost:3000'));
6. Insecure Data Storage
Problem: Storing sensitive data, like passwords or personal information, without encryption or secure storage methods can make it easy for attackers to steal this data if they gain access.
Solution:
- Encrypt Sensitive Data: Use encryption for sensitive data at rest. For example, use libraries like bcrypt for hashing passwords.
- Use HTTPS for Data in Transit: Encrypt data in transit by forcing HTTPS connections. Services like Let’s Encrypt offer free SSL certificates to secure your application.
const express = require('express');
const csurf = require('csurf');
const cookieParser = require('cookie-parser');
const app = express();
// Use cookie parser and csrf middleware
app.use(cookieParser());
app.use(csurf({ cookie: true }));
// Middleware to add CSRF token to all responses
app.use((req, res, next) => {
res.locals.csrfToken = req.csrfToken();
next();
});
app.get('/form', (req, res) => {
// Render a form with the CSRF token
res.send(`
`);
});
app.post('/submit', (req, res) => {
res.send('Data received securely!');
});
app.listen(3000, () => console.log('Server running on http://localhost:3000'));
7. Server-Side Vulnerabilities
Problem: Since Node.js runs on the server, any unhandled errors or improperly configured server settings can lead to security issues.
Solution:
- Error Handling: Always handle errors gracefully, and avoid exposing sensitive information in error messages. Instead of sending detailed error messages, use generic messages in production.
- Limit Request Size: Large payloads can overload your server, so limit the request body size using middleware like body-parser to prevent attacks like denial of service (DoS).
- Run as Non-Root User: Avoid running your application with root privileges. In the event of a compromise, this can help limit the damage an attacker can do.
Final Tips
Securing your Node.js and JavaScript applications takes time, but it’s a necessary investment. Here are some final quick tips:
- Use HTTPS Everywhere: Encrypting data in transit is critical to protect user data.
- Avoid eval() and similar functions: Functions like eval() can execute arbitrary code, making your app vulnerable to injection attacks. Avoid using them whenever possible.
- Keep Dependencies to a Minimum: Only install packages you really need. Each package introduces a potential vulnerability, so be selective.
By following these tips and regularly updating your knowledge on security practices, you’ll be better equipped to keep your Node.js applications safe. Security is an ongoing process, but with a proactive approach, you can significantly reduce your application’s vulnerability footprint.
Conclusion
As much as we aim to secure our code, the truth is there's no such thing as a perfectly secure application, and we can’t kill every vulnerability. New vulnerabilities are discovered regularly, libraries are updated, and our code constantly evolves. Security is an ongoing process that requires vigilance, consistent updates, and a proactive reverse engineering mindset.
Here are a few additional ways to keep improving your code security:
Regularly Review Code: Conduct code reviews with a focus on security. Peer reviews help catch vulnerabilities that one developer might miss.
Automate Security Testing: Use CI/CD pipelines with automated security testing to catch issues early in development. Tools like GitHub Dependabot, Snyk, and npm audit can be integrated into your workflow for continuous scanning.
Stay Informed: Security threats evolve, so stay updated with security news, libraries, and practices. Following communities like OWASP and the Node.js security team can keep you informed of the latest threats and mitigation techniques.
Least Privilege Principle: Limit permissions and access levels in your app and database. The principle of least privilege ensures that each part of your application only has the access it absolutely needs to function, reducing potential damage from a breach.
User Education: Encourage safe practices, especially for teams with access to sensitive code and environments. Developer security training can help avoid common mistakes that lead to vulnerabilities.
By being vigilant and continuously learning, you’ll be better equipped to manage security risks in the fast-paced Node.js ecosystem. Remember: it’s about reducing risk, not achieving perfection. Happy coding, and here’s to safer, more secure applications!
The above is the detailed content of How to Kill Vulnerabilities in Your Node.js App: A Guide to Writing Secure JavaScript Code. For more information, please follow other related articles on the PHP Chinese website!
 Replace String Characters in JavaScriptMar 11, 2025 am 12:07 AM
Replace String Characters in JavaScriptMar 11, 2025 am 12:07 AMDetailed explanation of JavaScript string replacement method and FAQ This article will explore two ways to replace string characters in JavaScript: internal JavaScript code and internal HTML for web pages. Replace string inside JavaScript code The most direct way is to use the replace() method: str = str.replace("find","replace"); This method replaces only the first match. To replace all matches, use a regular expression and add the global flag g: str = str.replace(/fi
 Custom Google Search API Setup TutorialMar 04, 2025 am 01:06 AM
Custom Google Search API Setup TutorialMar 04, 2025 am 01:06 AMThis tutorial shows you how to integrate a custom Google Search API into your blog or website, offering a more refined search experience than standard WordPress theme search functions. It's surprisingly easy! You'll be able to restrict searches to y
 8 Stunning jQuery Page Layout PluginsMar 06, 2025 am 12:48 AM
8 Stunning jQuery Page Layout PluginsMar 06, 2025 am 12:48 AMLeverage jQuery for Effortless Web Page Layouts: 8 Essential Plugins jQuery simplifies web page layout significantly. This article highlights eight powerful jQuery plugins that streamline the process, particularly useful for manual website creation
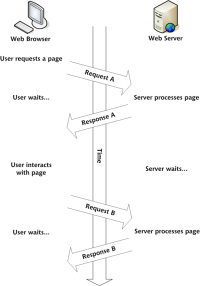 Build Your Own AJAX Web ApplicationsMar 09, 2025 am 12:11 AM
Build Your Own AJAX Web ApplicationsMar 09, 2025 am 12:11 AMSo here you are, ready to learn all about this thing called AJAX. But, what exactly is it? The term AJAX refers to a loose grouping of technologies that are used to create dynamic, interactive web content. The term AJAX, originally coined by Jesse J
 What is 'this' in JavaScript?Mar 04, 2025 am 01:15 AM
What is 'this' in JavaScript?Mar 04, 2025 am 01:15 AMCore points This in JavaScript usually refers to an object that "owns" the method, but it depends on how the function is called. When there is no current object, this refers to the global object. In a web browser, it is represented by window. When calling a function, this maintains the global object; but when calling an object constructor or any of its methods, this refers to an instance of the object. You can change the context of this using methods such as call(), apply(), and bind(). These methods call the function using the given this value and parameters. JavaScript is an excellent programming language. A few years ago, this sentence was
 10 Mobile Cheat Sheets for Mobile DevelopmentMar 05, 2025 am 12:43 AM
10 Mobile Cheat Sheets for Mobile DevelopmentMar 05, 2025 am 12:43 AMThis post compiles helpful cheat sheets, reference guides, quick recipes, and code snippets for Android, Blackberry, and iPhone app development. No developer should be without them! Touch Gesture Reference Guide (PDF) A valuable resource for desig
 Improve Your jQuery Knowledge with the Source ViewerMar 05, 2025 am 12:54 AM
Improve Your jQuery Knowledge with the Source ViewerMar 05, 2025 am 12:54 AMjQuery is a great JavaScript framework. However, as with any library, sometimes it’s necessary to get under the hood to discover what’s going on. Perhaps it’s because you’re tracing a bug or are just curious about how jQuery achieves a particular UI
 How do I create and publish my own JavaScript libraries?Mar 18, 2025 pm 03:12 PM
How do I create and publish my own JavaScript libraries?Mar 18, 2025 pm 03:12 PMArticle discusses creating, publishing, and maintaining JavaScript libraries, focusing on planning, development, testing, documentation, and promotion strategies.


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Safe Exam Browser
Safe Exam Browser is a secure browser environment for taking online exams securely. This software turns any computer into a secure workstation. It controls access to any utility and prevents students from using unauthorized resources.

PhpStorm Mac version
The latest (2018.2.1) professional PHP integrated development tool

MinGW - Minimalist GNU for Windows
This project is in the process of being migrated to osdn.net/projects/mingw, you can continue to follow us there. MinGW: A native Windows port of the GNU Compiler Collection (GCC), freely distributable import libraries and header files for building native Windows applications; includes extensions to the MSVC runtime to support C99 functionality. All MinGW software can run on 64-bit Windows platforms.

WebStorm Mac version
Useful JavaScript development tools

mPDF
mPDF is a PHP library that can generate PDF files from UTF-8 encoded HTML. The original author, Ian Back, wrote mPDF to output PDF files "on the fly" from his website and handle different languages. It is slower than original scripts like HTML2FPDF and produces larger files when using Unicode fonts, but supports CSS styles etc. and has a lot of enhancements. Supports almost all languages, including RTL (Arabic and Hebrew) and CJK (Chinese, Japanese and Korean). Supports nested block-level elements (such as P, DIV),





