It is not good news that strangers access your computer stealthily. How to check if someone is remotely accessing your computer? How to tackle the data leak or data loss issue? This post from MiniTool gives you corresponding suggestions.
Remote access is a convenient tech for workers at different locations. However, remote access scams come with malicious aims, such as stealing credential information on the computer, downloading malware secretly, or doing other operations. Fortunately, you have several approaches to check if someone is remotely accessing your computer. Keep reading and check your computer carefully.
Way 1. Check Recent Activities
Hackers remote access your computer with targets and operations will leave you traces. You can check the recent computer activities to tell if your computer is being accessed remotely.
- Check recently opened files/applications: Press Win E to open Windows Explorer on your computer where you can browse the recently accessed files. Click on the Windows icon to see the recently opened apps.
- View browser history/downloads: Open browsers on your computer to check the browsing history and download list. You should ensure that all the visited websites and downloaded items are made by yourself.
- Check login events: Press Win R to open the Run windows, then type eventvwr and press Enter to open Event Viewer. Head to Windows Logs > Security to check if there is someone attempting to log into your computer at an unusual time.
Way 2. View Programs via Task Manager
You can also check if someone is remotely accessing your computer by reviewing the programs in Task Manager. Programs may be remotely installed or accessed on your computer and run secretly. In this case, Task Manager is a good utility to check program status on your computer.
Press Ctrl Shift Esc to open Task Manager directly. Browse all the programs under the Processes tab. If there are any programs that are not installed or running by yourself, keep alert and check the application folder on your computer. You can seek help from professional computer services to remove suspicious software.
Way 3. Verify Windows Firewall Settings
Windows Firewall is a reliable and trustworthy tool that blocks unauthorized access to your computer effectively. Therefore, those remote access scammers may alter the Windows Firewall settings to ease their access.
Type Windows Defender Firewall with Advanced Security into the Windows Search bar and hit Enter to open the window. You need to look through the inbound and outbound rules. If there are dubious rules, click on them and choose Disable Rule at the right sidebar. Before deleting the rule, you are advised to verify the authorization and legitimation of the rule.

Way 4. Perform a Virus Scan
An alert window may prompt up when the Windows utilities detect remote access to your computer. When you get such a message, perform a virus scan to avoid underlying viruses on the computer. You can use reliable third-party antivirus software or run a Windows-embedded utility, such as Windows Security.
Tips: Stop Someone from Accessing Your Computer Remotely
It is necessary to learn how to check if someone is remotely accessing your computer. You should also know tactics to stop someone from accessing your computer. Here are some suggestions:
- Disable remote connections: To reject all remote connections, you can disable the remote connection by opening System Properties and ticking the Don’t allow remote connections to this computer option. Afterward, click Apply > OK to save the change.
- Change passwords: If your computer has already been remotely accessed, you need to change all the passwords of your crucial accounts on another security device. This measure can prevent further threats.
- Use a VPN: A Virtual Private Network (VPN) can hide your actual location and encrypt your data, which is a secure network connection option. You can choose an authorized VPN, like MiniTool VPN, and get it from its official website.
- Back up files regularly: Some malicious software or ransomware may delete or lock your crucial files. If you have any backups, you can get back your data without paying for it. MiniTool ShadowMaker is a robust backup software that supports file backup, folder backup, partition backup, and disk backup. You can try the trial edition to use the backup features for free for 30 days.
Final Words
Cybercrimes occur in diverse forms. You should always keep alert in daily use and check if someone is remotely accessing your computer from time to time to ensure a secure environment for computer use.
The above is the detailed content of How to Check If Someone Is Remotely Accessing Your Computer. For more information, please follow other related articles on the PHP Chinese website!
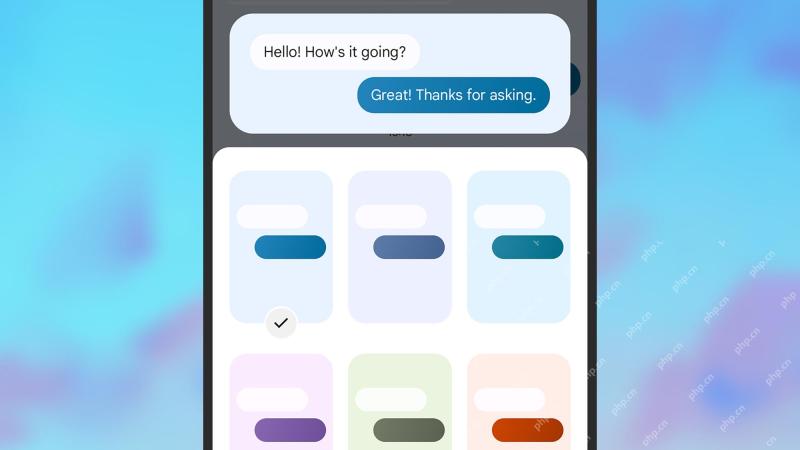 7 helpful Google Messages tips you need to knowApr 30, 2025 am 09:55 AM
7 helpful Google Messages tips you need to knowApr 30, 2025 am 09:55 AMMaster Google Messages: Seven Essential Tips and Tricks for Android Google Messages is the default texting app on most Android phones, handling SMS, MMS, and the advanced RCS (Rich Communication Services). RCS is now so prevalent it even works with
 Virtual Machine Detected in Roblox: Try the 4 Ways HereApr 29, 2025 pm 08:10 PM
Virtual Machine Detected in Roblox: Try the 4 Ways HereApr 29, 2025 pm 08:10 PMRoblox virtual machine detection errors and solutions Roblox users may experience an error "Virtual machine detected. Roblox cannot be used on virtual machines or virtual desktops". This error causes Roblox to crash. However, some user devices that encounter this error do not have virtual machines on them. If you also encounter this error, try the following: Method 1: Disable Hyper-V Hyper-V is Microsoft's virtualization product that allows you to create and run multiple virtual machines on a physical host. This utility can sometimes cause device problems, causing the application (such as Roblox) to run abnormally. Here is how to disable this feature: Step 1: Search on Windows
 Fixes on OneDrive Error Code 0x8004e4be in Windows 11/10Apr 29, 2025 pm 08:06 PM
Fixes on OneDrive Error Code 0x8004e4be in Windows 11/10Apr 29, 2025 pm 08:06 PMOneDrive error code 0x8004e4be: Troubleshooting and Solutions OneDrive, Microsoft's convenient file storage and synchronization service, can occasionally throw error code 0x8004e4be. This error typically disrupts login, sync operations, and overall c
 File Carving vs Metadata Recovery: A Brief Informative GuideApr 29, 2025 pm 08:05 PM
File Carving vs Metadata Recovery: A Brief Informative GuideApr 29, 2025 pm 08:05 PMFile Carving vs. Metadata Recovery: Two Key Digital Forensics Techniques This post compares file carving and metadata recovery, two vital file recovery methods in digital forensics. We'll explore their differences and when to use each. File Carving:
 The Scanner Is in Use or Unavailable? Here Are Some FixesApr 29, 2025 pm 08:04 PM
The Scanner Is in Use or Unavailable? Here Are Some FixesApr 29, 2025 pm 08:04 PMEpson Scanner Error E1460-B305: Troubleshooting Guide The Epson scanner error code E1460-B305 typically indicates the scanner is busy or inaccessible. This guide provides solutions to resolve this common issue. Understanding the Error The E1460-B305
 How to fix Windows update error 0x80240025?Apr 29, 2025 pm 08:00 PM
How to fix Windows update error 0x80240025?Apr 29, 2025 pm 08:00 PMWindows Update error code 0x80240025 explained Windows Update error code 0x80240025 can take place when your system fails to install updates because of limited
 The Elder Scrolls IV Oblivion Remastered Audio Not Working: FixedApr 29, 2025 pm 06:01 PM
The Elder Scrolls IV Oblivion Remastered Audio Not Working: FixedApr 29, 2025 pm 06:01 PMIs your Elder Scrolls IV: Oblivion Remastered audio malfunctioning? Experiencing crackling, distortion, or complete silence? This can seriously impact gameplay. This guide offers solutions to fix this frustrating problem. Audio Problems in Elder Scr
 Clair Obscur: Expedition 33 Fatal Error? Fix with 4 WaysApr 28, 2025 pm 08:02 PM
Clair Obscur: Expedition 33 Fatal Error? Fix with 4 WaysApr 28, 2025 pm 08:02 PMEncountering a "Clair Obscur: Expedition 33" fatal error can be frustrating, preventing the game from launching. This guide offers four solutions to resolve this issue. Clair Obscur: Expedition 33 Fatal Error Solutions Many players experien


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

SublimeText3 Linux new version
SublimeText3 Linux latest version

MantisBT
Mantis is an easy-to-deploy web-based defect tracking tool designed to aid in product defect tracking. It requires PHP, MySQL and a web server. Check out our demo and hosting services.

Safe Exam Browser
Safe Exam Browser is a secure browser environment for taking online exams securely. This software turns any computer into a secure workstation. It controls access to any utility and prevents students from using unauthorized resources.

SAP NetWeaver Server Adapter for Eclipse
Integrate Eclipse with SAP NetWeaver application server.

Zend Studio 13.0.1
Powerful PHP integrated development environment







