
How to add active permissions to Mycelium cold wallet
Mycelium cold wallet provides a feature called "active permissions" that allows users to Keep private keys while authorizing others to transact on their behalf. Here’s how to add active permissions to your Mycelium cold wallet:
Step 1: Create a cold address in Mycelium wallet
- Open the Mycelium wallet.
- Click on the "Wallet" tab and select "New Wallet".
- Select the "Cold Wallet" option and follow the prompts to create a new address.
- Create a strong password for your cold address.
Step 2: Update Firmware
- Make sure your Mycelium cold wallet is updated to the latest firmware.
Step 3: Connect the cold wallet
- Connect the cold wallet to your computer using a USB cable.
- In the Mycelium wallet, click on the "Settings" tab and select "Devices".
- Select "Connect Device" and follow the prompts to connect your cold wallet.
Step 4: Enable Active Permissions
- In the Mycelium wallet, click on the "Security" tab and select "Active Permissions".
- Click the "Enable Active Permissions" button.
- Enter your cold address password.
- Follow the on-screen prompts to complete the activation process.
Note:
- When active permissions are added, other authorized devices or applications will be able to conduct transactions on behalf of your cold wallet.
- Grant active permissions carefully and only to people or devices you trust.
- Always use a strong password to protect your cold wallet.
The above is the detailed content of How to add active permissions to Mycelium cold wallet. For more information, please follow other related articles on the PHP Chinese website!
 amazon project kuiper satellite launchApr 10, 2025 pm 05:36 PM
amazon project kuiper satellite launchApr 10, 2025 pm 05:36 PMAmazon's Project Kuiper satellite launch was postponed due to unfavorable weather conditions. The delay was likely influenced by factors such as high-altitude wind shear, lightning threats, and high surface winds, which are common hazards in space launches. This postponement highlights the need for meticulous planning and flexibility in the unpredictable environment of space operations.
 Is Wall Street Quietly Backing Solana? $42 Million Bet Says YesApr 10, 2025 pm 12:43 PM
Is Wall Street Quietly Backing Solana? $42 Million Bet Says YesApr 10, 2025 pm 12:43 PMA group of former Kraken executives acquired U.S.-listed company Janover, which secured $42 million in venture capital funding to begin building a Solana (SOL) treasury.
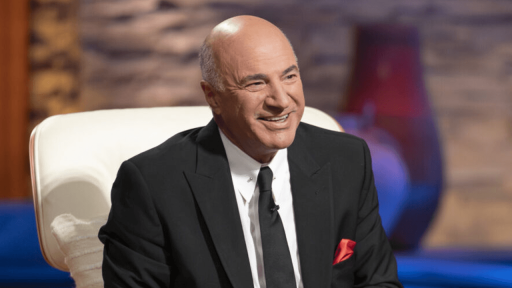 Kevin O'Leary Urges Trump to Impose 400% Tariff on Chinese GoodsApr 10, 2025 pm 12:35 PM
Kevin O'Leary Urges Trump to Impose 400% Tariff on Chinese GoodsApr 10, 2025 pm 12:35 PMCanadian businessman and investor Kevin O’Leary urged the Trump administration to impose a 400% tariff on Chinese goods, arguing that the current 104% tariff is insufficient to compel China to follow trade rules. O’Leary said these statements prior t
 Regulatory roadblocks are crumbling as the U.S. Treasury signals a sweeping pivot toward blockchain, stablecoins, and digital assetsApr 10, 2025 pm 12:27 PM
Regulatory roadblocks are crumbling as the U.S. Treasury signals a sweeping pivot toward blockchain, stablecoins, and digital assetsApr 10, 2025 pm 12:27 PMU.S. Treasury Secretary Scott Bessent laid out a broad financial reform agenda at the Bankers Association Summit on April 9, pledging to remove regulatory barriers
 China and Russia Have Started to Settle Some Trade Deals Using BitcoinApr 10, 2025 pm 12:19 PM
China and Russia Have Started to Settle Some Trade Deals Using BitcoinApr 10, 2025 pm 12:19 PMAccording to a report by VanEck, China and Russia have started to settle some trade deals using Bitcoin.
 Skybridge Capital's founder warns China is preparing fierce economic retaliation as the U.S. slaps 125% tariffs on Chinese goods, signaling currency shocks, massive stimulus, and financial warfare.Apr 10, 2025 pm 12:03 PM
Skybridge Capital's founder warns China is preparing fierce economic retaliation as the U.S. slaps 125% tariffs on Chinese goods, signaling currency shocks, massive stimulus, and financial warfare.Apr 10, 2025 pm 12:03 PMucci Outlines 5-Point Forecast on China's Next Moves Amid Rising Trade Tensions
 Ethereum (ETH) Underperforms Bitcoin (BTC)Apr 10, 2025 pm 12:01 PM
Ethereum (ETH) Underperforms Bitcoin (BTC)Apr 10, 2025 pm 12:01 PMunderperformed Bitcoin on 85% of all trading days since it launched in 2015. The ETH/BTC ratio, which tracks the value of Ether relative to Bitcoin, dropped to a five-year low of 0.018
 President Trump's Tariff Announcement Sent Bitcoin Dropping 5.4%Apr 10, 2025 am 11:53 AM
President Trump's Tariff Announcement Sent Bitcoin Dropping 5.4%Apr 10, 2025 am 11:53 AMIn the world of cryptocurrencies, few events can shake things up like big government decisions. President Trump's recent tariff announcement did exactly that

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

MantisBT
Mantis is an easy-to-deploy web-based defect tracking tool designed to aid in product defect tracking. It requires PHP, MySQL and a web server. Check out our demo and hosting services.

ZendStudio 13.5.1 Mac
Powerful PHP integrated development environment

SublimeText3 Chinese version
Chinese version, very easy to use

PhpStorm Mac version
The latest (2018.2.1) professional PHP integrated development tool

SecLists
SecLists is the ultimate security tester's companion. It is a collection of various types of lists that are frequently used during security assessments, all in one place. SecLists helps make security testing more efficient and productive by conveniently providing all the lists a security tester might need. List types include usernames, passwords, URLs, fuzzing payloads, sensitive data patterns, web shells, and more. The tester can simply pull this repository onto a new test machine and he will have access to every type of list he needs.





