
Ensuring the security of full stack applications is paramount to protect user data, maintain trust, and comply with regulations. In this guide, we explore essential security best practices and techniques to safeguard your applications.
Why Security Matters
Security breaches can have severe consequences, including data theft, service disruptions, and damage to reputation. Adopting robust security practices mitigates risks and enhances the resilience of your applications.
Essential Security Best Practices
Authentication and Authorization
- Implement Secure Authentication: Use industry-standard protocols like OAuth 2.0 or OpenID Connect for authentication. Example using Passport.js with JWT:
// Example using Passport.js with JWT for authentication
const passport = require('passport');
const passportJWT = require('passport-jwt');
const JWTStrategy = passportJWT.Strategy;
const ExtractJWT = passportJWT.ExtractJwt;
const User = require('../models/user');
passport.use(new JWTStrategy({
jwtFromRequest: ExtractJWT.fromAuthHeaderAsBearerToken(),
secretOrKey: 'your_secret_key'
},
async (jwtPayload, done) => {
try {
const user = await User.findById(jwtPayload.id);
if (!user) {
return done(null, false, { message: 'User not found' });
}
return done(null, user);
} catch (err) {
return done(err);
}
}
));
- Role-Based Access Control (RBAC): Implement granular access controls based on user roles and permissions to limit privileges and reduce the impact of potential breaches.
Data Protection
Encrypt Sensitive Data: Encrypt sensitive information (e.g., passwords, credit card details) both at rest and in transit using strong encryption algorithms (e.g., AES-256).
Secure APIs: Validate input, sanitize data, and use HTTPS with TLS (Transport Layer Security) to protect data integrity and confidentiality.
Secure Coding Practices
Avoid Common Vulnerabilities: Follow secure coding guidelines to mitigate risks such as SQL injection, cross-site scripting (XSS), and cross-site request forgery (CSRF).
Regular Security Audits: Conduct regular code reviews, security assessments, and penetration testing to identify and address vulnerabilities proactively.
Sample Code: Securing API Endpoints with Express and JWT
// middleware/auth.js
const jwt = require('jsonwebtoken');
const config = require('../config');
const User = require('../models/user');
function verifyToken(req, res, next) {
const token = req.headers['authorization'];
if (!token) {
return res.status(403).json({ message: 'Token not provided' });
}
jwt.verify(token, config.secret, async (err, decoded) => {
if (err) {
return res.status(401).json({ message: 'Unauthorized' });
}
req.userId = decoded.id;
const user = await User.findById(decoded.id);
if (!user) {
return res.status(404).json({ message: 'User not found' });
}
next();
});
}
module.exports = verifyToken;
Conclusion
Implementing robust security measures is essential for protecting your full stack applications from threats and vulnerabilities. By adopting the best practices and techniques outlined in this guide, you can enhance the security posture of your applications and safeguard sensitive data effectively.
Next, we will delve into the principles and advantages of building real-time applications using WebSockets.
The above is the detailed content of Security Best Practices. For more information, please follow other related articles on the PHP Chinese website!
 From C/C to JavaScript: How It All WorksApr 14, 2025 am 12:05 AM
From C/C to JavaScript: How It All WorksApr 14, 2025 am 12:05 AMThe shift from C/C to JavaScript requires adapting to dynamic typing, garbage collection and asynchronous programming. 1) C/C is a statically typed language that requires manual memory management, while JavaScript is dynamically typed and garbage collection is automatically processed. 2) C/C needs to be compiled into machine code, while JavaScript is an interpreted language. 3) JavaScript introduces concepts such as closures, prototype chains and Promise, which enhances flexibility and asynchronous programming capabilities.
 JavaScript Engines: Comparing ImplementationsApr 13, 2025 am 12:05 AM
JavaScript Engines: Comparing ImplementationsApr 13, 2025 am 12:05 AMDifferent JavaScript engines have different effects when parsing and executing JavaScript code, because the implementation principles and optimization strategies of each engine differ. 1. Lexical analysis: convert source code into lexical unit. 2. Grammar analysis: Generate an abstract syntax tree. 3. Optimization and compilation: Generate machine code through the JIT compiler. 4. Execute: Run the machine code. V8 engine optimizes through instant compilation and hidden class, SpiderMonkey uses a type inference system, resulting in different performance performance on the same code.
 Beyond the Browser: JavaScript in the Real WorldApr 12, 2025 am 12:06 AM
Beyond the Browser: JavaScript in the Real WorldApr 12, 2025 am 12:06 AMJavaScript's applications in the real world include server-side programming, mobile application development and Internet of Things control: 1. Server-side programming is realized through Node.js, suitable for high concurrent request processing. 2. Mobile application development is carried out through ReactNative and supports cross-platform deployment. 3. Used for IoT device control through Johnny-Five library, suitable for hardware interaction.
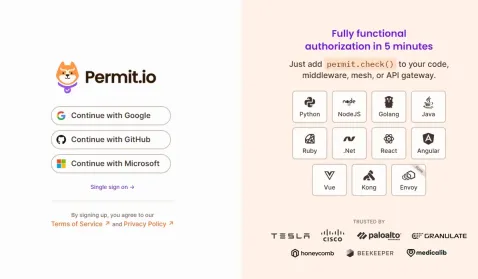 Building a Multi-Tenant SaaS Application with Next.js (Backend Integration)Apr 11, 2025 am 08:23 AM
Building a Multi-Tenant SaaS Application with Next.js (Backend Integration)Apr 11, 2025 am 08:23 AMI built a functional multi-tenant SaaS application (an EdTech app) with your everyday tech tool and you can do the same. First, what’s a multi-tenant SaaS application? Multi-tenant SaaS applications let you serve multiple customers from a sing
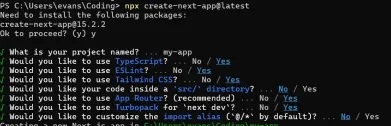 How to Build a Multi-Tenant SaaS Application with Next.js (Frontend Integration)Apr 11, 2025 am 08:22 AM
How to Build a Multi-Tenant SaaS Application with Next.js (Frontend Integration)Apr 11, 2025 am 08:22 AMThis article demonstrates frontend integration with a backend secured by Permit, building a functional EdTech SaaS application using Next.js. The frontend fetches user permissions to control UI visibility and ensures API requests adhere to role-base
 JavaScript: Exploring the Versatility of a Web LanguageApr 11, 2025 am 12:01 AM
JavaScript: Exploring the Versatility of a Web LanguageApr 11, 2025 am 12:01 AMJavaScript is the core language of modern web development and is widely used for its diversity and flexibility. 1) Front-end development: build dynamic web pages and single-page applications through DOM operations and modern frameworks (such as React, Vue.js, Angular). 2) Server-side development: Node.js uses a non-blocking I/O model to handle high concurrency and real-time applications. 3) Mobile and desktop application development: cross-platform development is realized through ReactNative and Electron to improve development efficiency.
 The Evolution of JavaScript: Current Trends and Future ProspectsApr 10, 2025 am 09:33 AM
The Evolution of JavaScript: Current Trends and Future ProspectsApr 10, 2025 am 09:33 AMThe latest trends in JavaScript include the rise of TypeScript, the popularity of modern frameworks and libraries, and the application of WebAssembly. Future prospects cover more powerful type systems, the development of server-side JavaScript, the expansion of artificial intelligence and machine learning, and the potential of IoT and edge computing.
 Demystifying JavaScript: What It Does and Why It MattersApr 09, 2025 am 12:07 AM
Demystifying JavaScript: What It Does and Why It MattersApr 09, 2025 am 12:07 AMJavaScript is the cornerstone of modern web development, and its main functions include event-driven programming, dynamic content generation and asynchronous programming. 1) Event-driven programming allows web pages to change dynamically according to user operations. 2) Dynamic content generation allows page content to be adjusted according to conditions. 3) Asynchronous programming ensures that the user interface is not blocked. JavaScript is widely used in web interaction, single-page application and server-side development, greatly improving the flexibility of user experience and cross-platform development.


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

VSCode Windows 64-bit Download
A free and powerful IDE editor launched by Microsoft

Dreamweaver CS6
Visual web development tools

WebStorm Mac version
Useful JavaScript development tools

Safe Exam Browser
Safe Exam Browser is a secure browser environment for taking online exams securely. This software turns any computer into a secure workstation. It controls access to any utility and prevents students from using unauthorized resources.

Zend Studio 13.0.1
Powerful PHP integrated development environment





