
Understanding Supply Chain Attacks
Supply chain attacks occur when a malicious actor infiltrates your software's development or deployment process, introducing vulnerabilities through third-party components, dependencies, or even through compromised development tools. These attacks can have devastating consequences, leading to widespread security breaches and data theft.
Best Practices to Prevent Supply Chain Attacks
1. Audit Dependencies Regularly
Regularly auditing your project's dependencies is crucial. Use tools like npm audit, Snyk, or OWASP Dependency-Check to identify and address vulnerabilities in third-party libraries.
npm audit
Ensure your project uses the latest versions of dependencies, and avoid using deprecated or unmaintained libraries.
2. Lock Dependencies
Use a lock file (package-lock.json or yarn.lock) to ensure consistent dependency versions across different environments. This helps prevent unintended updates that could introduce vulnerabilities.
npm install --save-exact <package> </package>
3. Verify Package Integrity
Verify the integrity of packages using tools like Subresource Integrity (SRI) for CDN-hosted libraries and npm's shrinkwrap or yarn to lock down specific versions and checksums.
// Example in package-lock.json
"dependencies": {
"example-package": {
"version": "1.0.0",
"resolved": "https://registry.npmjs.org/example-package/-/example-package-1.0.0.tgz",
"integrity": "sha512-..."
}
}
4. Implement Security Policies
Implement security policies like Content Security Policy (CSP) to mitigate the impact of any injected malicious scripts.
<meta http-equiv="Content-Security-Policy" content="default-src 'self'; script-src 'self' https://trusted-cdn.com;">
5. Use Code Signing
Code signing helps ensure the integrity and origin of your code. By signing your code, you can verify that it hasn't been tampered with.
#Example with GPG gpg --sign --detach-sign --armor <file> </file>
6. Monitor for Suspicious Activity
Monitor your development and deployment environments for any suspicious activity. Tools like GitHub's Dependabot can help by automatically updating dependencies and alerting you to vulnerabilities.
Real-World Example: Event-Stream Incident
One notable supply chain attack was the Event-Stream incident. In 2018, a popular npm package, Event-Stream, was compromised. The attacker added malicious code to steal Bitcoin wallets. This incident highlighted the importance of maintaining control over your dependencies and the risks of using third-party code without proper vetting.
Conclusion
Preventing supply chain attacks requires a proactive approach to security. By auditing dependencies, locking versions, verifying package integrity, implementing security policies, using code signing, monitoring for suspicious activity, and educating your team, you can significantly reduce the risk of such attacks.
Securing your JavaScript projects is an ongoing process, but with these best practices, you can build a robust defense against supply chain threats. Stay vigilant, and keep your software supply chain secure.
Stay updated on the latest security trends and tools by following industry blogs, participating in security forums, and continuously improving your security practices. Together, we can make the web a safer place.
The above is the detailed content of Preventing Supply Chain Attacks in JavaScript. For more information, please follow other related articles on the PHP Chinese website!
 Replace String Characters in JavaScriptMar 11, 2025 am 12:07 AM
Replace String Characters in JavaScriptMar 11, 2025 am 12:07 AMDetailed explanation of JavaScript string replacement method and FAQ This article will explore two ways to replace string characters in JavaScript: internal JavaScript code and internal HTML for web pages. Replace string inside JavaScript code The most direct way is to use the replace() method: str = str.replace("find","replace"); This method replaces only the first match. To replace all matches, use a regular expression and add the global flag g: str = str.replace(/fi
 Custom Google Search API Setup TutorialMar 04, 2025 am 01:06 AM
Custom Google Search API Setup TutorialMar 04, 2025 am 01:06 AMThis tutorial shows you how to integrate a custom Google Search API into your blog or website, offering a more refined search experience than standard WordPress theme search functions. It's surprisingly easy! You'll be able to restrict searches to y
 Example Colors JSON FileMar 03, 2025 am 12:35 AM
Example Colors JSON FileMar 03, 2025 am 12:35 AMThis article series was rewritten in mid 2017 with up-to-date information and fresh examples. In this JSON example, we will look at how we can store simple values in a file using JSON format. Using the key-value pair notation, we can store any kind
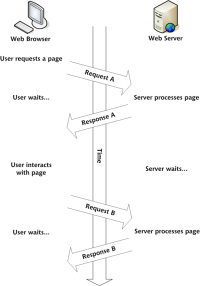 Build Your Own AJAX Web ApplicationsMar 09, 2025 am 12:11 AM
Build Your Own AJAX Web ApplicationsMar 09, 2025 am 12:11 AMSo here you are, ready to learn all about this thing called AJAX. But, what exactly is it? The term AJAX refers to a loose grouping of technologies that are used to create dynamic, interactive web content. The term AJAX, originally coined by Jesse J
 10 jQuery Syntax HighlightersMar 02, 2025 am 12:32 AM
10 jQuery Syntax HighlightersMar 02, 2025 am 12:32 AMEnhance Your Code Presentation: 10 Syntax Highlighters for Developers Sharing code snippets on your website or blog is a common practice for developers. Choosing the right syntax highlighter can significantly improve readability and visual appeal. T
 8 Stunning jQuery Page Layout PluginsMar 06, 2025 am 12:48 AM
8 Stunning jQuery Page Layout PluginsMar 06, 2025 am 12:48 AMLeverage jQuery for Effortless Web Page Layouts: 8 Essential Plugins jQuery simplifies web page layout significantly. This article highlights eight powerful jQuery plugins that streamline the process, particularly useful for manual website creation
 What is 'this' in JavaScript?Mar 04, 2025 am 01:15 AM
What is 'this' in JavaScript?Mar 04, 2025 am 01:15 AMCore points This in JavaScript usually refers to an object that "owns" the method, but it depends on how the function is called. When there is no current object, this refers to the global object. In a web browser, it is represented by window. When calling a function, this maintains the global object; but when calling an object constructor or any of its methods, this refers to an instance of the object. You can change the context of this using methods such as call(), apply(), and bind(). These methods call the function using the given this value and parameters. JavaScript is an excellent programming language. A few years ago, this sentence was
 10 JavaScript & jQuery MVC TutorialsMar 02, 2025 am 01:16 AM
10 JavaScript & jQuery MVC TutorialsMar 02, 2025 am 01:16 AMThis article presents a curated selection of over 10 tutorials on JavaScript and jQuery Model-View-Controller (MVC) frameworks, perfect for boosting your web development skills in the new year. These tutorials cover a range of topics, from foundatio


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

WebStorm Mac version
Useful JavaScript development tools

SublimeText3 Linux new version
SublimeText3 Linux latest version

ZendStudio 13.5.1 Mac
Powerful PHP integrated development environment

SublimeText3 Mac version
God-level code editing software (SublimeText3)

SublimeText3 English version
Recommended: Win version, supports code prompts!






